|
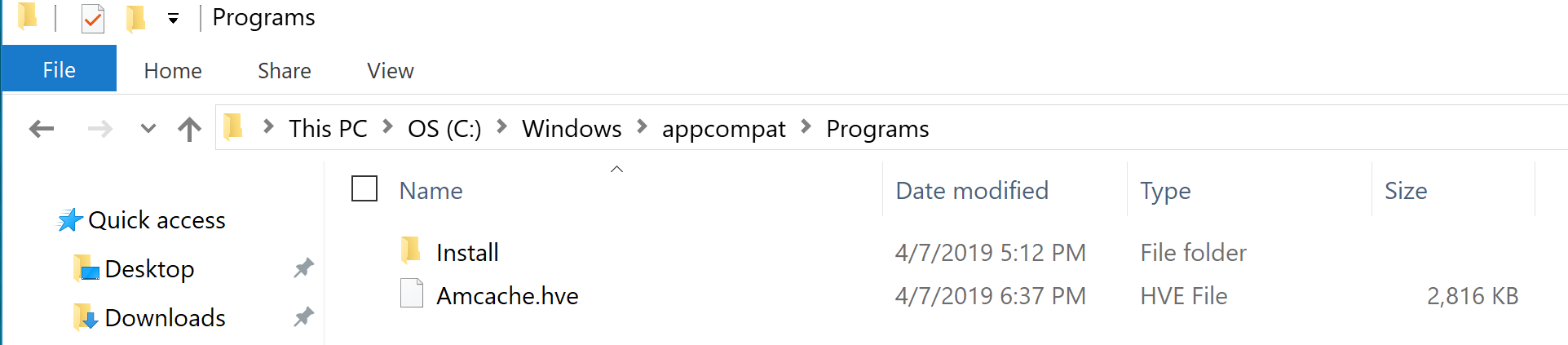
Shimcache/Amcache is also know is AppCompatCache. There are certain application which are build to work on the historical version of the OS. Usually if an application needs 'shimming' - windows looks at AppCompatKey registry key to figure out if an application needs shimming or not. When a program is shimmed, a registry key is updated to notify the system. Use tools like RegRipper to parse it.
Forensics Value: If you are dealing with an Anti-forensics kind of situation. The adversary might have deleted the logs from prefetch and the file itself. The amcache entries will show if the app existed on the system. Key things to remember:
Shimcache/Amcache and Prefetch is a very powerful combination for identification of the execution. Things to keep in mind during shimcache analysis: 1) Each time an exe is modified or renamed - it'll create a new shimcache entry 2) Cannot determine the last time of execution via Shimcache. Antedating: Creating a document with incorrect time stamps.
Investigation:
How to antedate a document?
Readings: http://www.cse.scu.edu/~tschwarz/COEN252_13/Papers/antedating.pdf Prefetch Basics: Windows Prefetch stores application specific data in order to help it to start quicker. Each time you turn on your computer, Windows keeps track of the way your computer starts and which programs you commonly open. Windows saves this information as a number of small files in the prefetch folder. The next time you turn on your computer, Windows refers to these files to help speed the start process.
The os loads key pieces of data and code from disk into memory before it's actually needed. Location: c:\Windows\Prefetch Prefetch Investigation FAQ: When you should grab prefetch file? You can grab is before performing Incident Response as the prefetch directory is populated after the application is executed. The content of the file is pretty volatile. How you can use it in an Investigation? Analysis of prefetch file is common in investigation, it has wealth of information stored in it. * It contains:
Here is what information we can glean from the prefetch:
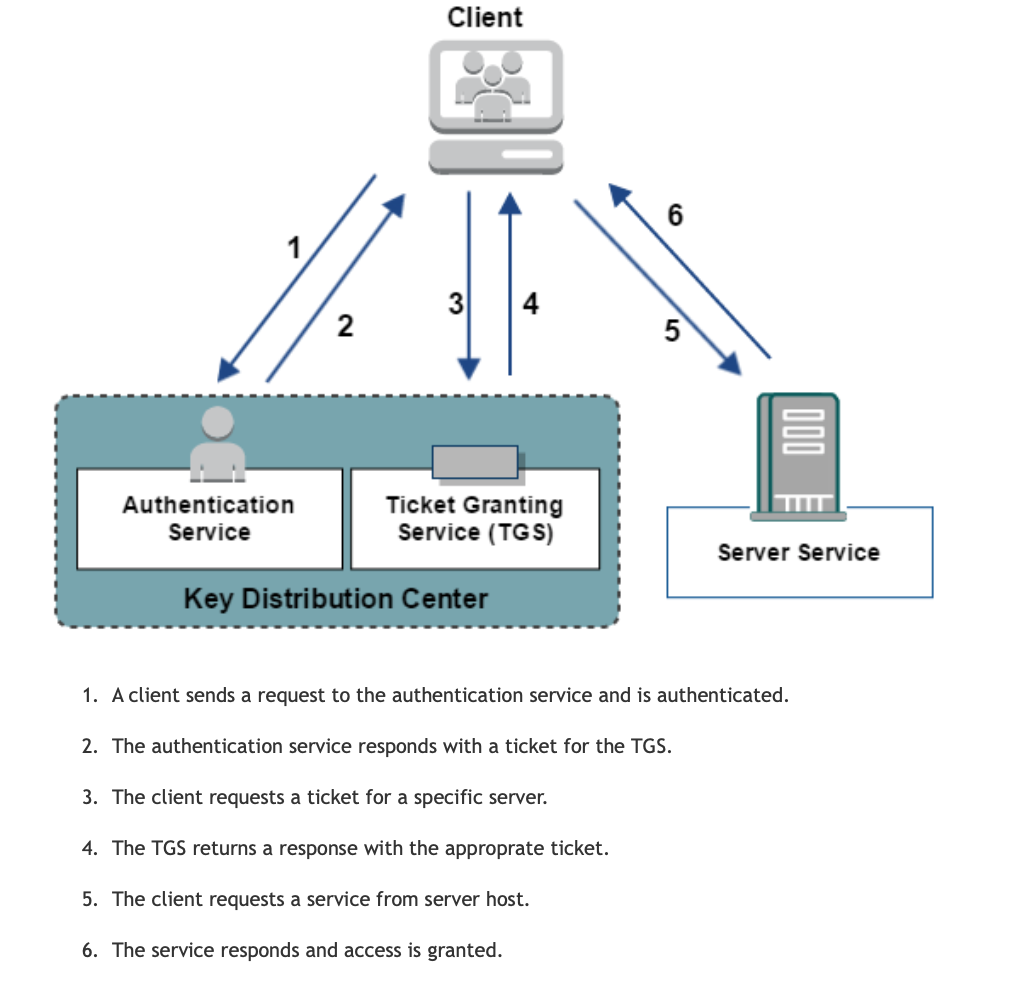
 Kerberos is a network authentication protocol inspired by the greek work for a a three heaed dog Cerberus. Couple of key points to remember about the protocol
Source: https://docops.ca.com/ca-single-sign-on/12-8/en/configuring/policy-server-configuration/authentication-schemes/configure-kerberos-authentication Kerberos Attacks#Pass the ticket:
Ways to investigate Pass the ticket Attack
Countermeasures:
In overpass-the-hash, the attacker will try to capture NTLM hash for the account it wishes to compromise using tools like Mimikatz etc. Using this command in mimikatz: Sekurlsa::pth /user:[USER] /domain:[DOMAIN] /ntlm:[NTLM HASH] The NTML hash was passed into Kerberos authentication provider using RC4 Encryption #Kerberoasting: The focus of this attack is to compromise a service account. It request a ticket for a highly privileged service account. Capture the hash for it and crack it offline. #Golden Ticket: This is generated with a Ticket Granting Ticket for any account with my expiration is generated. Majority of the Active Directory based attacks can be detected by implementing Microsoft Advanced Threat Analytics. https://docs.microsoft.com/en-us/advanced-threat-analytics/what-is-ata |
Archives
September 2019
Categories
All
|
 RSS Feed
RSS Feed