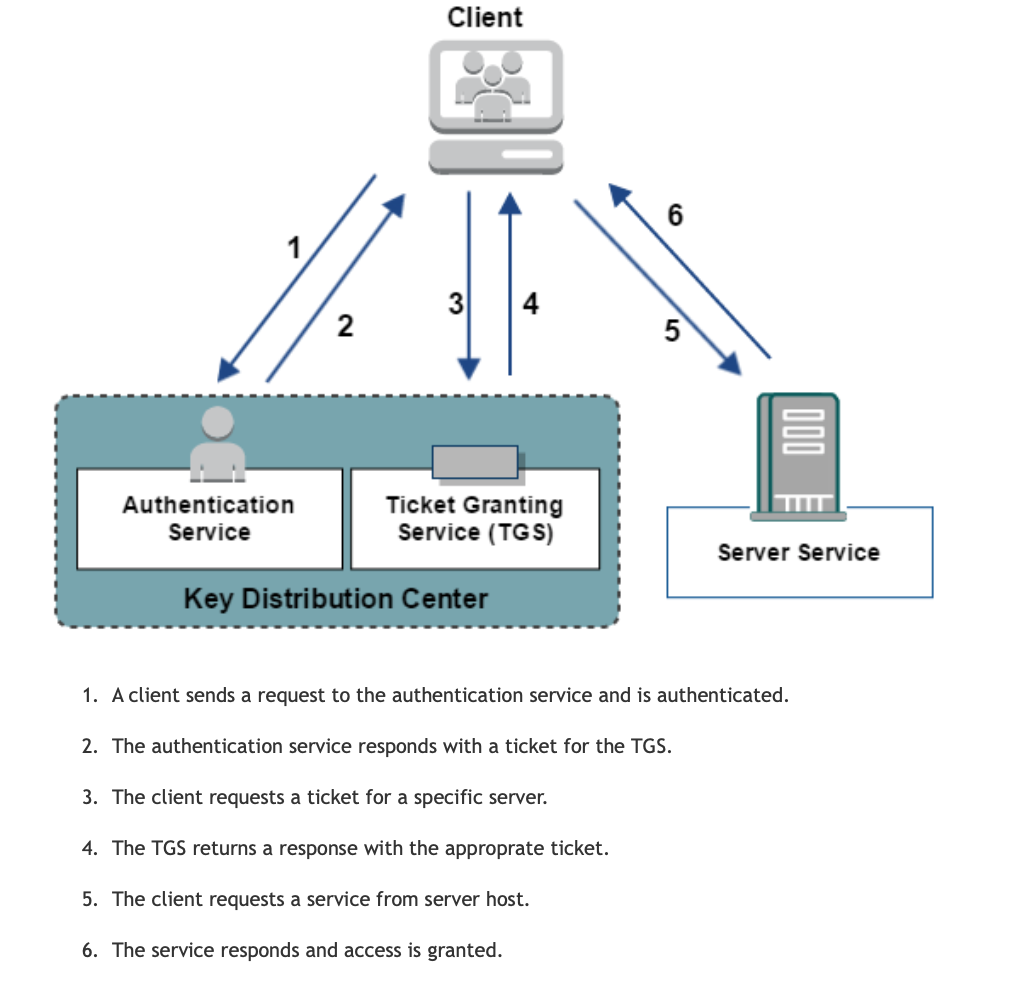
 Kerberos is a network authentication protocol inspired by the greek work for a a three heaed dog Cerberus. Couple of key points to remember about the protocol
Source: https://docops.ca.com/ca-single-sign-on/12-8/en/configuring/policy-server-configuration/authentication-schemes/configure-kerberos-authentication Kerberos Attacks#Pass the ticket:
Ways to investigate Pass the ticket Attack
Countermeasures:
In overpass-the-hash, the attacker will try to capture NTLM hash for the account it wishes to compromise using tools like Mimikatz etc. Using this command in mimikatz: Sekurlsa::pth /user:[USER] /domain:[DOMAIN] /ntlm:[NTLM HASH] The NTML hash was passed into Kerberos authentication provider using RC4 Encryption #Kerberoasting: The focus of this attack is to compromise a service account. It request a ticket for a highly privileged service account. Capture the hash for it and crack it offline. #Golden Ticket: This is generated with a Ticket Granting Ticket for any account with my expiration is generated. Majority of the Active Directory based attacks can be detected by implementing Microsoft Advanced Threat Analytics. https://docs.microsoft.com/en-us/advanced-threat-analytics/what-is-ata
profitcoin
4/28/2021 03:10:45 pm
FOR RECOVERY OF STOLEN BITCOIN / CRYPTOCURRENCY , RECOVERY OF LOST FUNDS FROM SCAMMER. Have you ever been a victim of a scam? or have you lost your money to fake hackers online? I implore you to contact this trustworthy hacker and recovery expert [email protected] , I was a victim of fake people posing as binary options and bitcoin investors, I lost a sum of $4,000 and 2BTC from my bitcoin wallet to these fakes. It took a while before I realized they were scams and this really hurt .Then an in-law of mine heard about it and recommended to me a specialist with the address - [email protected] .
Oliver Bangart
6/19/2022 03:14:00 am
We were in severe need of a loan to purchase a car for our family, but my application was denied due to my poor credit score. My credit score was 564 (Transunion), 588 (Equifax), and 591 (Experian) when I checked it. There were several bad entries. After reading so many internet reviews, I decided to go for ROOTKITS CREDIT SPECIALIST as they were highly rated. They assisted me in erasing all of the negative aspects of my life, and increasing my score to excellent across all bureaus and also created good trade lines; they completed all of this within 9 days. You can get in touch with them via: Comments are closed.
|
Archives
September 2019
Categories
All
|
 RSS Feed
RSS Feed