|
We will discuss about Windows Credentials Theft in the blog post. This is the first thing any attacker will do after exploiting to your network. The aim of the attacker will be to gather the credentials for privilege escalation and lateral movement. Companies do not pay much attention to the account and password management and adversaries do take advantage of it. See the mind-map below to understand the top categories.
Kiaan
1/23/2020 11:13:45 am
I started using WISETECHHACKER (AT) DOT COM services since Jan 6th and am happy to tell the world today to get in contact with wisetechhacker@gmail. com for any form of hacking services. Am talking from experience they deliver smooth and clean jobs without any trace God bless you wisetechhacker. i never regretted my contact with them.
James
5/19/2021 03:07:15 pm
I invested a lot of money to earn profits trading, and lost my investments to a scam company. I have now had all my investments and profits returned by a recovery commando. You can reach me to share my trading experience and how I had all my money returned jameswillliams04 at gmail dot com
ellissa Rockwell
9/2/2021 06:38:19 am
Thanks to the Evolution of Blockchain Forensics it is now possible to Recover your lost Bitcoin from Scammers all you need to do is Hire a professional recovery expert to help you get the job done. i was able to recover 40,000USD worth of bitcoin i lost to a fake investment website thanks to ""FastRecovery02 Hat (G) (M A) I)(L) Come""" he is a professional recovery expert and hacker that helped recover my fund Without Charging an Up Front Payment. he take charges only after the job is done. he is the best in the market and he always get the job done.
kadem
9/8/2021 02:54:45 pm
investment and crypto fraud are on the rise and lost of people are falling victim of these scam everyday, i happen to be a victim as well but i was able to get my funds back thanks to FÅSTŘËČÕVËŘÝ02 DÕT ČÕMË.. He is a professional recovery expert and hacker that helped recover my BTC Without an Up Front Payment. he take charges only after the job is done. he is the best in the market and he always get the job done.
Berlin
9/9/2021 05:47:12 am
Please beware there are many fake bitcoin mining/clouding out there, I have been a victim once but now a certified blockchain consultant and I know better. The whole plan was so smooth I could not doubt it. Bitcoin is actually a great investment option but one thing I discovered over time is that it is not possible to mine bitcoin so don’t be deceived. I invested $25000 on a particular website called eurekaminingblock, I monitored the profit yielding but was told to open a new blockchain account to receive my payout. A public wallet was imported into the account and I was made to believe that was my profit. The bitcoin was labelled non spendable and it took me 2 years to be able to access it without the knowledge of the company. The non spendable bitcoin is the scam out there now and a lot of people are falling victim of it. I found 5TRACK RECOVERY on Quora who helped me access my investment together with the profit without the knowledge of the company.
Natasha Robinson
9/11/2021 06:34:03 am
Words cannot express my gratitude. Credit brainiac was upfront and got to work immediately. I had used other credit repair services before and all they did was take my money. Credit brainiac was the best choice i made! I was completely uneducated about my rights as well as how many errors truly can be on your credit report. These things significantly hurt you when trying to purchase a vehicle or home. My daughter had some health problems younger and i had over 60 medical bad reporting on my credit. Even though creditors say medical isn’t really frowned upon, this was killing my score and credibility. One week after reaching c r e d i t b r a i n i a c.r e p a i r at qmail d[]t ( o m for help, i had no negative reporting on my credit anymore, not even one. Very professional!
Ariel Monas
10/17/2021 03:33:54 pm
A promise keeper deserve high regard ,I want to use this medium to compliment a special Tech Team with High regard , as for me they're the BEST ,cause I have tried 2 separate companies for recovery & nothing came out till I hired PERFECTWALLETRECOVERY dot come I checked there web and later had to send all my troubling situation to perfect wallet recovery hhat g m a i ! and the rest is JOY now.
zee
10/17/2021 03:56:29 pm
.Reach out to perfect wallet recovery HART GEE MALE to help you ,and you will be so glad you did so, best believe, there web is perfect wallet recovery dot come.
first
11/22/2021 08:28:39 pm
if you so happen to fall or have fallen victim of ŠČÄMMËŘŚ or your BÍŤČÕÍÑ was ŠŤÕĹËÑ and you'd like to ŘËĆÖVËŘ your lost Funds, send an ËMÄÏĻ to FÅSTŘËČÕVËŘÝ02 HÃŤ GMÃÍĹ ČÕMË he is a professional ŘËČÕVËŘÝ Agent that specializes in ŘËĆÖVËŘÍÑG ŠŤÕĹËÑ HÄČKËD ŠČÄMMËD BÍŤČÕÍÑ or MONEY ŠŤÕĹËÑ from your account
Bryson Remington
12/15/2021 02:30:11 am
I’m very fortunate to have c r e d i t b r a i n i a c.r e p a i r at gmail d[]t ( o m take care of my credit. I feel that this was really worth more than the money i put into this to have my credit restored. I’ve been able to secure a mortgage and my credit score has increased significantly. Very fast and efficient hacker. I look forward to Credit Brainiac helping other people I will be referring their way.
Kyle Copeland
2/8/2022 09:45:35 am
I had 112 negative items listed on my credit report. The majority of items were student loans with late payments. CreditBrainiac.Repair <<>> gmail <<>> (om was able to fix my credit from 630 to 841 and all the negative items were wiped off my Experian, Equifax and TransUnion reports.!! That allowed me to buy my first house with a phenomenal interest rate. His hacking service is priceless, it is the best money you will ever spend! I am now more confident than I have ever been before.
James Barrow
3/1/2022 12:58:20 pm
[email protected]
James Barrow
3/1/2022 01:00:02 pm
This Turkey American hacker by the name WORLDHACKERS79@ GMAIL COM we can help you change your driving records and clear some implicating records you had online. This is no joke, we helped and it has worked for a lot of people,If you are in need of a professional hacker, Worldhackers79@gmail. com is the man for the job. Other services he offers are below::
Desmond Stones
5/12/2022 05:13:18 pm
Do you know you can have all tracking information of your suspected cheating spouse on your palm and at your convenience? It's amazing and I'll say this spy app is a type of app you can use to keep track of your partner's phone without them realizing. Although searching for the best surveillance app on the web may provides varied options, including using an extra hand to get problem solved. Yes, using extra hand like contacting the best and most reliable tech guy on (Remotespytech(@)gmailcom), I can affirm that it's such a great deal. We all know thoughts of infidelity in relationships isn't a new thing and can eventually cause a great havoc if not handle with care and utmost discipline, which is why we needed experts who are the best at what they do to handle the collection of information discreetly without causing any harm. When I saw review of a lady, showering praises on how she got into her spouse's device getting all evidences that he's been a cheat and was able to leave the toxic relationship before it gets late, it turns out it was the help of this same guy, I hope you find this piece of information very useful and reach him today...
Ellis Johnson
7/2/2021 04:25:20 pm
I trust anonymous credit repairer and i stand by them with everything I have. I was not disappointed and i believe that they work each case/customer with the professionalism and knowledge of getting the job done just like they did on my credit. I recommend them to anyone who needs fast and good results with all seriousness. Thank you a n o n y m o u s c re d i t r e p a i r e r .g. mail com. I owe them a lot more with what they have done for me.
Adams Good
5/12/2022 05:14:19 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Amanda Hobden
9/1/2021 01:09:19 pm
To Recover your Lost Bitcoin what you need do is Hire a Professional to get the Job done' ''''''5TRACKRECOVERY'' @ g m a i l has the fastest recovery so far. Note; very very few People are capable of Recovering Bitcoin, be Careful not to Hire Scammers pretending to be Recovery Expert, as they will also scam you of your Funds.
Victor
9/7/2021 08:26:17 pm
I'd like to hire 5trackrecovery but how do i know he's legit?
Amanda
9/9/2021 05:41:32 am
ETHICAL HACKER (5TRACK RECOVERY HAT (G) M A I L ARE THE FASTEST FOR ALL RECOVERY SERVICES
Adams Good
5/12/2022 05:15:19 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
mike
9/8/2021 03:00:15 pm
You can Recover Your lost Bitcoin by Hiring a Professional to get the job done, Bitcoin Recovery Requires Unique Hacking Skill that only a hand full of hackers Possess. 99% of Recovery Websites out there are Operated by scammers in order to make the scam Look legit. Hire a trusted hacker to recover your funds By Visiting FÅSTŘËČÕVËŘÝ02 DÕT ČÕMË.. A Recovery expert who RECOVER $58K WORTH OF BTC I LOST BITCOIN mining scam. AS GUARANTY HE TAKES CHARGES ONLY AFTER THE JOB IS DONE
Sam
10/4/2021 10:55:50 am
I am enquiring once Fastrecovery02 retrieved your funds how they got the funds to you? was it through an escrow or directly to you? Did you have to pay anything at the release time out of pocket? Thank you so much. Once you fall victim to bitcoin scam trusting anyone is terrifying.
Adams Good
5/12/2022 05:16:07 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Raymond Wright
9/9/2021 05:37:45 am
I have lose money finding my 4btc lost in the wind till PERFECT WALLET RECOVERY . COME was recommended, they are Ethical Hackers skillful & Experienced ,NO UPFRONT PAYMENT and there Recovery software is the BADDEST ,contact by EMAILING PERFECT WALLET RECOVERY HAT (G) MALE,Highly Ranked service
Demon
9/9/2021 06:12:56 am
I'm deeply impressed to hear someone talk about PERFECT WALLET RECOVERY . COM ,HIS recovery is everywhere. Good experts are rare like him
Ariel Monas
10/17/2021 03:40:13 pm
I hired 2 other tech earlier before i finally meet Agent Billy PERFECT WALLET RECOVERY dort COM, his super good,. no doubt as for me his better of any other tech firms out there...Just in a week,his forensic team work out my recovery of 82 USD grand. It's never a joke to be rich again.
Ariel
11/1/2021 12:56:20 am
Raymond are you wrote rhis message?Please answer.I think perfect wallet recovery is scam people of their money.
Ariel Monas
11/1/2021 11:16:18 am
Raymond are you really hired perfect wallet recovery and they did all jobs for you.I see here comment that i never leaved about perfect wallet recovery.I am still whaiting for payment from him.Are he is legit or not?
Adams Good
5/12/2022 05:17:10 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Everest Perry
10/27/2021 06:33:06 pm
.Good news!!!1 Good news!!!!! you can recover all you lost through this authentic steps . Visit - PERFECT WALLET RECOVERY (.) COME , I recommend perfect wallet recovery (what s app - +1 (731) 474 1973
Adams Good
5/12/2022 05:25:44 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
JOSHUA WOODS
12/27/2021 06:42:51 pm
Adams Good
5/12/2022 05:26:09 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Joey
1/9/2022 06:53:38 am
I was so ripped off on binary options while trying to get my life savings multiplied. I was confused on what I could do to get my money back because I already read online that going to a lawyer or any chargeback company wouldn't help. After so many research and help requests from friends, I later after a while luckily bumped into a website "HACKSANDRECOVERY DOT NET" in the process of my online research, I went through the website and saw they help recover funds from binary options scam, cryptocurrency scam, etc. I took the risk and contacted the website's admin, I explained the whole situation to him, how the investment went and the binary options brokers I dealt with. He assured me that I would get my money back but it would take just little time. He requested for all the details about the brokers that scammed me and also about the amount I invested, I provided all and kept hoping on God. Luckily for me after some time, he was able to recover nearly 85% of my lost funds into my local bank account I provided to him, I was highly amazed because I felt all was lost already. I advise you visit the website "HACKSANDRECOVERY DOT NET" now also if you need to recover your funds from any scam broker 2/9/2022 10:26:49 am
Perfect recovery of lost funds follow this LINK :
Mills Dachin
2/26/2022 06:03:38 pm
In 2021, scammers made off with $14B in ill-gotten crypto. So, a lot.
James Barrow
3/1/2022 12:57:00 pm
This Turkey American hacker by the name WORLDHACKERS79@ GMAIL COM we can help you change your driving records and clear some implicating records you had online. This is no joke, we helped and it has worked for a lot of people,If you are in need of a professional hacker, Worldhackers79@gmail. com is the man for the job. Other services he offers are below::
Exploit World
4/1/2022 01:42:21 pm
LEGIT FULLZ & TOOLS STORE
Desmond Stones
5/12/2022 05:12:07 pm
Do you know you can have all tracking information of your suspected cheating spouse on your palm and at your convenience? It's amazing and I'll say this spy app is a type of app you can use to keep track of your partner's phone without them realizing. Although searching for the best surveillance app on the web may provides varied options, including using an extra hand to get problem solved. Yes, using extra hand like contacting the best and most reliable tech guy on (Remotespytech(at)gmailcom), I can affirm that it's such a great deal. We all know thoughts of infidelity in relationships isn't a new thing and can eventually cause a great havoc if not handle with care and utmost discipline, which is why we needed experts who are the best at what they do to handle the collection of information discreetly without causing any harm. When I saw review of a lady, showering praises on how she got into her spouse's device getting all evidences that he's been a cheat and was able to leave the toxic relationship before it gets late, it turns out it was the help of this same guy, I hope you find this piece of information very useful and reach him today...
Wizard Harry
5/8/2020 12:53:15 am
Need To Hire A Hacker❓ Then contact WIZARDHARRY✅
recoverlife
6/28/2021 10:17:06 am
wizard harry is a scam. he quote $2500 to help me recover funds with crypto currency and knew i was scammed out of my lifesavings but he kept asking for more and more. at the end i lost 11k to him and never recovered a dime. if you want to keep losing and being scammed then ask him for help. 5/23/2020 04:23:03 am
BITCOIN, BINARY OPTION: Please everyone should be careful and stop being fooled by all these brokers and account managers, they scammed me over $70,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, at the end, i lost all my money. All efforts to reach out to their customer support desk was declined, i found it very hard to move on. God so kind i followed a broadcast that teaches on how scammed victims can recover their fund, i contacted the email provided for consultation ([email protected]) ,i got a feedback after some hours and i was asked to provide all legal details concerning my investment,i did exactly what they instructed me to do without delay, to my greatest surprise i was able to recover my money back including my profit which my capital generated. I said i will not hold this to myself but share it to the public so that all scammed victims can get their funds back, look at wizard Harry skill's on site.. https://goranagren18.wixsite.com/website
tony lee
8/3/2020 02:25:35 am
hello
Greg Derrick
8/17/2020 07:20:53 pm
I want to use this medium in appreciating Perfect Hidden hacker, after being ripped off my money, he helped me find my cheating lover he helped me hack her WhatApp, Gmail and Kik and I got to know that she was cheating on me, in less than 24 hours he helped me out with all the information I needed to see, Perfect Hidden hacker is trustworthy and affordable contact him on email: ([email protected])
Donald Charlotte
8/18/2020 07:00:49 pm
I started suspecting my partner not long ago but I had no concrete evidence, then I was recommended to this professional Perfect hacker email ([email protected]) He helped me to expose all my partner’s secrets by hacking into my partner’s phone & social media accounts at a very affordable price.
John scofield
9/8/2020 11:20:50 am
Have you ever needed an expert when it comes to hacking? Have you ever wanted to hack someone’s email account? Recover lost accounts,school grade,boost credit score? Do you need to find a person’s sensitive information? Do you want to invade a person’s PayPal, Skrill, Amazon, Facebook or any other site account? Upgrade of University Grades,Password and email Retrieval, phone Lines monitoring, Skype Accounts, Hack Social Network, Trace calls on real time conversations, Remove Criminal Records, Credit Fixing, cyber-crime investigation, Hack Bank Accounts, Identification of Cheating Partner or employee,GET HOT STOCK TIPS Then contact contact Email:- [email protected] Hangout :- [email protected] Telegram Number +14242742967 Business Whatsapp :- 1 (925) 291-0054) Text Message/Call: +1 424) 274 2967 or click on this link to chat on whatsapp https://wa.me/message/REE2BBXU4CEYF1 10/18/2020 05:50:08 am
It seemed like a mistake that has ruined my life, i would have lost up to 180000 Dollars in deposits, not to talk of how much I've grown the account, Thank to being relentless and hopeful , i came Across a set of consultant and attorneys who have currently helped me recover 100000 dollars, recovery is ongoing and transparent. In case you also need help, reach out to: wizardcharles1 @ gmail
Jason Spangler
9/18/2021 02:48:53 am
I was taken advantage of during my investment into cryptocurrency as I fell into the wrong hands and $40,000 was stolen from me in bitcoin. I almost gave up as I was told it was not not traceable neither is it possible to recover then I saw an article about a technology guru named Dennis Walker .. I contacted him and worked with him and to my surprise he was able to recover $32,580 I was so happy I decided to share this for anyone who might be in need of such assistance please write him on dennisdfixer at gm ail. com
Deborah Mandy Fox
10/29/2020 03:33:33 pm
Hi.I ran over a by and large incredible Software engineer Goatse Security. They have helped with a huge load of issues like Phone Hack, Record Hack, Clear Commitments, Assessment update, criminal records help E.t.c They have saved my life, Contact: [email protected]
scott
10/30/2020 10:43:44 am
I have been through a lot of shit just because the one i love decided to treat me wrong, i have been in the dark for a very long time knowing my fiance is cheating on me but i have no evidence, so i decided to tell a a friend and he introduced me to a hacker i will say shadownethacker is a savior, he hacked into my Fiance's phone and now i receive a copy of every single text that drop on her phone and her WhatsApp notifications/msgs cloned on my phone, i can't keep this to myself this guy is amazing, you might want to try him, to be convinced contact them via: [email protected] or whatsapp him on +1 (781) 312-9232 11/10/2020 12:22:26 am
BITCOIN, BINARY OPTION: Please everyone should be careful and stop being fooled by all these brokers and account managers, they scammed me over $200,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, in the end, I lost all my money. All efforts to reach out to their customer support desk had declined, I found it very hard to move on. God so kind I followed a broadcast that teaches on how scammed victims can recover their fund, I contacted the email provided for consultation, I got feedback after some hours and I was asked to provide all legal details concerning my investment, I did exactly what they instructed me to do without delay, to my greatest surprise I was able to recover my money back including my profit which my capital generated. I said I will not hold this to myself but share it to the public so that all scammed victims can get their funds back, ::::::: if you have problems on any stuffed like a bank, company, examinations, database, Social media hacks, Email hacks, Phone hacks, Bitcoin hacks, increased Credit score boost to 800, School result upgrading, Binary option funds recovery Instagram, Bitcoin Mining, WhatsApp, Twitter, Monitor your colleague, access your spouse social media, and a lot more: Email. ( [email protected] ) 11/10/2020 12:29:06 am
BITCOIN, BINARY OPTION: Please everyone should be careful and stop being fooled by all these brokers and account managers, they scammed me over $200,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, in the end, I lost all my money. All efforts to reach out to their customer support desk had declined, I found it very hard to move on. God so kind I followed a broadcast that teaches on how scammed victims can recover their fund, I contacted the email provided for consultation, I got feedback after some hours and I was asked to provide all legal details concerning my investment, I did exactly what they instructed me to do without delay, to my greatest surprise I was able to recover my money back including my profit which my capital generated. I said I will not hold this to myself but share it to the public so that all scammed victims can get their funds back, ::::::: if you have problems on any stuffed like a bank, company, examinations, database, Social media hacks, Email hacks, Phone hacks, Bitcoin hacks, increased Credit score boost to 800, School result upgrading, Binary option funds recovery Instagram, Bitcoin Mining, WhatsApp, Twitter, Monitor your colleague, access your spouse social media, and a lot more: Email. ( contact@wizardcharlesgrouphackers. com ) 11/10/2020 12:30:43 am
BITCOIN, BINARY OPTION: Please everyone should be careful and stop being fooled by all these brokers and account managers, they scammed me over $200,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, in the end, I lost all my money. All efforts to reach out to their customer support desk had declined, I found it very hard to move on. God so kind I followed a broadcast that teaches on how scammed victims can recover their fund, I contacted the email provided for consultation, I got feedback after some hours and I was asked to provide all legal details concerning my investment, I did exactly what they instructed me to do without delay, to my greatest surprise I was able to recover my money back including my profit which my capital generated. I said I will not hold this to myself but share it to the public so that all scammed victims can get their funds back, ::::::: if you have problems on any stuffed like a bank, company, examinations, database, Social media hacks, Email hacks, Phone hacks, Bitcoin hacks, increased Credit score boost to 800, School result upgrading, Binary option funds recovery Instagram, Bitcoin Mining, WhatsApp, Twitter, Monitor your colleague, access your spouse social media, and a lot more: Email. ( [email protected] )
michael smith
11/28/2020 10:27:06 am
Salvatore Perez
5/7/2021 07:46:31 am
The truth is that there's no quick fix for your credit unless you have a good computer guru to help and lucky for me I met Dennis after a few wrong contacts that couldn't get the job done, Dennis was referred to me by my uncle when I was bitterly battling with my report and derogatoriness. My score went from low 460 to 810 with no negatives and debts.. I was so happy I had to come put him out here for who ever might be in need. Reach him on dennisdfixer at gmail com or nine one seven .. Seven two two .. Six nine one three.
If you are looking for a professional hacker to provide hacking solutions on
GARETT TWAINE
12/7/2020 04:22:02 am
Life has taught me that you can’t control someone’s loyalty. No matter how good you are to them it doesn’t mean that they will treat you the same way. I have been married to my husband for years with no idea he was cheating. Suddenly i started noticing changes in behavior, i suspected something was wrong. So i confided in a friend who convinced and introduced me to the Mr White. He was able to hack into my husband mobile phone, Text messages, Call logs, IG, browser history, deleted messages, Emails and WhatsApp . It seemed as though my life was spinning out of control getting to find out he has someone else. I filed for a divorce just could not continue with lies. If you feel you are been exploited in your marriage and you need proof. I suggest you contact WhitehatstechATgmailDOTcom him for your spy and hacking job and be free, just like me today.They are just so amazing, also clear my credit cards debts and because of these set of superior WHITECOLLAR HACKERS I am here living my best life. 12/8/2020 06:01:46 pm
Are you interested in the service of a hacker to get into a phone, facebook account, snapchat, Instagram, yahoo, Whatsapp, get verified on any social network account, increase your followers by any amount, bank wire and bank transfer. 12/20/2020 12:48:44 pm
This is overwhelming to share here, I almost lost my trust in Hackers after being scammed 5 times I met a friend on the road whose car got breakdown and give him a lift and after some discussion, he gave me a good professional hacker contact who helped me to recover back my company funds that were lost to online hackers who break into my company software and took all the banking information and divert all our clients, Wizard Harry is an excellent hacker with 100% trust, it took him 24 hours and all my company lost funds of $2.54M was restored back and right now I now have a secured software that no hacker can access, all thanks to Wizard Harry. anyone looking for a trusted hacker I will refer you to contact him on [email protected]
recoverlife77
6/28/2021 10:19:14 am
wizard harry is a scam. he quote $2500 to help me recover funds with crypto currency and knew i was scammed out of my lifesavings but he kept asking for more and more. at the end i lost 11k to him and never recovered a dime. how did he recover 2.54 million for you in 24 hours? i only needed him to recover less than 200k and it took forever. this florence zuckerberg blog is fake. dont trust it. 1/2/2021 11:26:47 pm
Thanks to [email protected] who's contact i came across here, i hired him and he did so perfectly. I'm so thankful to him.
recoverlife77
6/28/2021 10:20:04 am
Henry,
cintra
1/3/2021 11:22:45 pm
If you need the services of a certified ethical hackers contact: [email protected]
grey john
1/8/2021 06:49:43 am
RELIABLE PRIVATE ONLINE INVESTIGATIONS Have you ever needed an expert when it comes to hacking? Have you ever wanted to hack someone’s email account? Recover lost accounts,school grade,boost credit score? Do you need to find a person’s sensitive information? Do you want to invade a person’s PayPal, Skrill, Amazon, Facebook or any other site account? Upgrade of University Grades,Password and email Retrieval, phone Lines monitoring, Skype Accounts, Hack Social Network, Trace calls on real time conversations, Remove Criminal Records, Credit Fixing, cyber-crime investigation, Hack Bank Accounts, Identification of Cheating Partner or employee,GET HOT STOCK TIPS Then contact contact Email:- [email protected] Hangout :- [email protected] Business Whatsapp :- +1 (925) 291-0054) or click on this link to chat on whatsapp https://wa.me/message/REE2BBXU4CEYF1
Lincoln Randall
1/13/2021 04:37:14 am
I was able to recover my funds from a very sketchy company, 24Options, Last year a friend and I invested all our life savings but got duped in the process. This January, we were able to use the services of R E C O V E R C O I N @ R E S C U E T E A M . C O M and we have gotten all our money back. My nightmare is over, It's a whole new day here. Do be careful when dealing with investments.
Kimberly Elvis
1/23/2021 08:56:35 am
It has been really hard losing a lot of my money to these binary options and cryptocurrency trading companies. Fortunately, I found a Recovery company that made sure I got back everything I lost. If you are in a similar situation and have lost a lot of money, Contact: R E C O V E R C O I N at R E S C U E T E A M dot C O M. they are reliable, fast and very good
Jose Goldman
1/25/2021 02:33:19 pm
I thank God I escaped from the scammers hands. I recently recovered my funds
Jade Baber
1/26/2021 04:37:48 pm
Thank you [email protected] I just confirmed the bad school grades you helped me in changing God bless you now I have peace of mind.. funny enough I never believed in [email protected] but here I am saying a big thank you to this hacker, I feel so so so blessed coming in contact with you thanks.
Colin Thompson
1/27/2021 02:51:07 am
I have read so many negative reviews about credit repair that I thought every company in the industry was a scam. A friend of mine had used Credit Specialist4 and told me that they did a great job. So, with caution, I contacted them and I was pleasantly surprised. They were very patient and set me up on a plan that was affordable for me. All in all I was very happy with their service and even more happy with my fantastic new credit score. I would recommend them to anyone looking for credit repair. Contact: (CR E D I T S P E C I A L I S T 4 at G M A I L dot C O M)
Richard Clark
1/27/2021 05:30:29 pm
I don't usually do this but i had to because of the amount of fake agents i ran into before i met Trojan. If you need a real Transunion, equifax expert to boost or rebuild your score, change your school grades etc this guy named Trojan is just the best out here and he did me a good job with getting my score to 800 and getting me off BK. you can contact him on (T R O J A N at W R I T E M E dot C O M)
Christina Farwell
1/28/2021 03:56:40 pm
Are you having difficulty in Accessing your bitcoin Wallet or falling a Victim to a Scammers due to one reason or the other. You can kneel on us for positive Result & Retrieve your lost fund back with %110 Assured. and we can also help you with University Grades. Loans. Wiping Criminal Records. iClouds Breaching YouTube and Phones Hacking!! For years they have stood as help to Individuals Organization to Secure and to Recover their lost Files/Password/ Bitcoin and funds etc. Contact: (F I X U R W O R R I E S at D O C T O R dot C O M)
Debra Dugan
1/30/2021 11:34:54 am
I started trading Crypto on Binary options, at first everything was going smoothly till I tried withdrawing. I was made to believe that I had to build my account to a certain point before withdrawing, I had lost a total sum of 10.000BTC. After weeks of turmoil and sadness that investment brought me and my family. I saw recommendations to hire RECOVER COIN RESCUE TEAM and I was lucky they helped me recover all of my funds without any hassle in less than 48 hours, I am so happy doing this because I know how many people would benefit from this useful information. Fortunately for me I was able to recover all I lost. (R E C O V E R C O I N at R E S C U E T E A M dot C O M) is a real refund professional feel free to reach out to them for a quick response if you're having similar issues.
Linda Robinson
2/20/2021 12:03:30 pm
My husband use to be a big time cheat i was very sure of this but i had no proof and i need something...just anything i could get my hands on as evidence so i don't sound stupid anytime i confront him about the women he often hides to talk to in his car or any other place where i wouldnt over hear their conversations.well I got a recommendation from an IT colleague at the office about a hacker from a hack network online. i got the contact of this hacker and sent him a message explain my situation to asking him if he could help me out, he politely replied and asked me for some information about my husband mobile device, no personal info was asked for also, i provided it all to him and in less than 24 hours i was getting too see my husband text messages, call logs and as well as whatsapp messages as they come into his phone, i was able to get good and solid proof for my lawyers to file a divorce, if you are having similar issues i would advice you contact him as well. i wish you the best. [email protected] .tell him LInda referred you.
alexander castro
3/1/2021 02:15:25 pm
Programmerade bankomater
CREDIT CARD
3/2/2021 10:42:20 am
Email:[email protected]
He was able to clear my debts and remove my hard inquiries and raise my score
He was able to clear my debts and remove my hard inquiries and raise my score 3/5/2021 02:59:22 am
Hello, i am Anne, am a single mother with 3 kids, I had tried severally in the past to boost my
Emerald Florence
3/5/2021 06:31:08 am
Please don't be a victim for imposters who claim that they are good hackers, I hired two different hackers to help me get my boyfriend phone clone and help me with the access to see his WhatsApp chat, these two different hacker fraud me and I had to reach out to Hacker Vladimir Levin after reading so much about him on google and he responded to my email with [email protected], after a brief illustration he went ahead and did the job within 4 hours. I'm so thankful for his help, I discovered the secret that has been going on, I could never have known about it if I didn't hire Vladimir Levin.
silver
3/9/2021 01:38:54 am
I strongly recommend the service of a GREAT RUSSIAN HACKER to you
Elisabeth Jakobsson
3/15/2021 03:34:32 pm
I met the best of all hackers his email is [email protected] this hacker made a way were there was non, I have been scammed by 2 hackers who promised to get my school grades fixed and yet they could not complete what they started but after a friend of mine directed me to [email protected] who has always worked for him when it comes to fixing of bad grades and other hacking services this hacker rendered’s I became interested to work with this hacker and am glad this hacker didn’t fail me.. all I heard about [email protected] was all real this hacker is legit and did a very smooth job for me
Franko Orsborn Donelrio
3/24/2021 07:28:08 pm
Talking about hiring a hacker regarding crypto invested capital lost without having back a cent of the capital is known and agreed to be fraud, so many trade site online today are placed on google just to rip off anyone who becomes a victim, I'm Officer Franko Orsbon Donelrio i knew about bitcoin few years ago and the bitcoin has only increased to 17k to 18k and then go back to 2k to 3k plus and it happened that i needed to go for peace keeping assignment, i used most of my funds to buy bitcoin and i was able to by 112 BTC, it happened that i came back 2019 December and i had some funds which was very enough to spend and that took my mind from my 112 BTC, a faithful day i was in a meeting and i saw some good investment i could invest in and wanted to buy a new home so i decide to log into my bitcoin wallet, unluckily for me i lost my password and i tried to reset it but nothing was working so i hired several hacker and they scammed me up to $40k so i decided to gave up on it but i was very lucky on this day 20.02.2021 i was able to get in touch with [email protected] who now help me to reset my password and enable me to withdraw my funds and he also recovered the 40k i lost, everything about him was amazing and excellent.
Grayson Liam
3/27/2021 01:23:11 pm
Have you given up on hacking just because you worked with wrong hackers? welcome to the vault hackers.we have a solid reputation and we have been invisible to authorities for decades and we will continue to be the best,we have a very strong firewall which means when we get your job done we leave no trace..we are good at what we do..we will also help you fish out fake hackers. 4/1/2021 05:30:11 am
If you are on this page You are probably a victim of a scam from a fraudulent company keep calm, we can help you ! we have a fast & effective solution to get your hard earned money back, Lost of Forex trading recovery, Lost of Cryptocurrency recovery, Bitcoin mining, Flipping cash, Deleting of criminal records, Clear Taxes, Increase your Credit score and top up balance, DMV database....WhatsApp: +1 (361) 201-2646 Visit our website read more about us : https://wizardcharlesgrouphackers.com/.n/
james SMITH
4/13/2021 07:34:26 am
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or
james SMITH
4/19/2021 03:55:36 pm
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or 4/25/2021 01:07:02 am
FOR RECOVERY OF STOLEN BITCOIN / CRYPTOCURRENCY , RECOVERY OF LOST FUNDS FROM SCAMMER. Have you ever been a victim of a scam? or have you lost your money to fake hackers online? I implore you to contact this trustworthy hacker and recovery expert [email protected] , I was a victim of fake people posing as binary options and bitcoin investors, I lost a sum of $4,000 and 2BTC from my bitcoin wallet to these fakes. It took a while before I realized they were scams and this really hurt .Then an in-law of mine heard about it and recommended to me a specialist with the address - [email protected] . He helped me recover my lost bitcoins in less than 72hrs and the fakes were caught and made to pay for what they did to me .if you have lost any amount to online scams and you're seeking to recover LOST FUNDS from wallet hackers, fake hackers, online dating scams, BTC wallet hack, recovery of lost funds from fake binary investors .Reach out to Wizard Charles Group Hackers to help you Visit website to read more about them : https://wizardcharlesgrouphackers.com/.n/
celien robin
4/25/2021 03:54:10 pm
I was researching online and I came across a glowing report of a beautiful hacker called Jamie in a trusted UK credit site. I am in the UK and I needed to improve my credit score because I couldn’t get approved for a car mortgage as a result of a poor credit score. I had medical bills, too many inquiries, charge offs, late payments and an eviction. Although Jamie lives in the united states however, as a credit repair specialist he promised to erase all the negative items influencing my credit profile negatively, replacing them with good lines of credit and eventually increase my score to a high 700 so I can be qualified for the car mortgage and even qualify for the new job I seek. Guess what happened after 7 business days - he actually did all he said he will do, deleted all the negative items and raised my score. My family and I are very happy now because I got the car mortgage and the new job. If anyone needs his or her credit fixed ASAP, whether in the Uk, Canada or US, Just run to him he will get the job done in a relatively short time. Here is his contact; creditrepairmannetwork at gmail dot com
profitcoin
4/27/2021 03:58:04 pm
FOR RECOVERY OF STOLEN BITCOIN / CRYPTOCURRENCY , RECOVERY OF LOST FUNDS FROM SCAMMER. Have you ever been a victim of a scam? or have you lost your money to fake hackers online? I implore you to contact this trustworthy hacker and recovery expert [email protected] , I was a victim of fake people posing as binary options and bitcoin investors, I lost a sum of $4,000 and 2BTC from my bitcoin wallet to these fakes. It took a while before I realized they were scams and this really hurt .Then an in-law of mine heard about it and recommended to me a specialist with the address - [email protected] . He helped me recover my lost bitcoins in less than 72hrs and the fakes were caught and made to pay for what they did to me .if you have lost any amount to online scams and you're seeking to recover LOST FUNDS from wallet hackers, fake hackers, online dating scams, BTC wallet hack, recovery of lost funds from fake binary investors .Reach out to Wizard Charles Group Hackers to help you
Jessica
4/30/2021 07:28:27 am
All these binary options, cryptocurrency and online investment companies are scams, I lost a total of $96k usd. Things have turned good for me, being able to recover my investments by a Recovery Pro. You can mail me if you are interested in the means I used to get my money back. mxspy01 at gmail
Wallace
5/2/2021 10:32:02 pm
Don’t be fooled please! I invested money, I made profit initially he was insisting me to deposit more money which I foolishly did. When I said I wanted to withdraw, they started giving excuses, delaying me and finally they blocked my account. I have all the emails, text messages they sent me. They aren’t regulated and they are just scammers, I have filed a report and sought the assistance of a private investigation firm mail mxspy01 (gmail) to get back my money. The guys at MXspy01 are dependable, to get your money or at least half back.
Roland McCain
5/12/2021 02:28:43 am
If you require professional help to recover your stolen cryptocurrency, or if it was sent to the wrong wallet address, hack your spouse’s phone remotely, contact [email protected] for assistance.
james SMITH
5/12/2021 07:27:29 am
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or
Vivian Loren
5/17/2021 06:38:23 pm
My trust in God is unshakable because i believed in him and he has been so good to me even when i was depressed so many by fakes hackers and imposters who claimed to be real and professional hackers/private investigators before i came across JAMES as he helped save a dying soul and being ripped off…I appreciate you so much James and i promise to always talk about you and your job delivery to the world instead of them being victims anymore…for you guys information he does all hacking related jobs ranging from Texts, What Sapp, Phone calls monitoring of day to day activities of cell phone, Viber ,Instagram, SCHOOL GRADES and Facebook..Just name it and it will be done cos he’s very honest and reliable. Contact him Via the following bellow….. EMAIL;Jamesethicalhacker[a]gmail. com TEXT,CALL: +1(775)374-4344 WHATSAPP ON :+1(775)374-4344 He’s the only Ethical hacker with guarantee that will provide result and won’t expose your confidential data to anyone because he work with discretion and deliver a perfect and untraceable job with 100% guarantee...
Sarah Jackson
5/17/2021 06:44:27 pm
Hi Everyone, Let me share this with you. When i really wanted to know what my Husband has been up to lately as I seems not to be getting his attention and i need confirmation as well as a hack into the only number he used with me solely for the past 5 years that would show many things proving his infidelity and cheating life style as well as other things of abuse. . Then i was introduce to this honest reliable and God fearing Hacker JAMES JONATHAN by a friend whom he helped with evidence and proof of cheating during her divorce. Infact, it was like a magic because he work with discretion and deliver and was able to hack into my husband’s cell phone so i could monitor his cell phone activities like Facebook, Snap chat, WhatsApp, Instagram,Text messages, Calls and above all gain me full access to his mobile phone and emails without touching his phone. I couldn’t help but to advertise his outstanding job status and delivery online and also introduce him to those who have their spouse cheating on them and want to spy on them and need evidence and proof but I would prefer to let his services speak for itself Contact him Via… EMAIL: Jamesethicalhacker[a]gmail.com TEXT, CALL: +1 775 374-4344 WHATSAP HIM +1 775-374-4344 and be happy forever. He will help you out with any hack related issues. His job is 100% undetectable and you will never regret contacting him because he’s honest ,genuine and truthful.
Legion Hacktivist Group
5/21/2021 03:23:57 am
Are you Seeking for a LEGIT HACKER Who Will Get Your Job Done Efficiently WithOut Upfront Payment?
JANET BRAX
5/22/2021 06:27:29 pm
I Have Used “[email protected]” Quite A Number Of Times And He Has Never Disappointed Me. He Has Once Help Me Get Proof On My Wife Cheating Activities On Her Phone . He Does All Types Of Mobile Hack;Get Unrestricted And Unnoticeable Access To Your Partner/Spouse/Anybodies 6/5/2021 06:02:37 am
Great Wizardcharles AT consultant DOT com has broken a world record by retrieving $18 million dollar worth bitcoin, this was reported by Stella a council member of the United State territory. Now that he has begun to grow famous around the globe we plead to anyone who comes across this comment to share with others to help those who have been scammed to get back their funds, they all can now reach Wizard Charles for help. WhatsApp the great wizard +971 55 274 0754 6/12/2021 03:38:59 am
I must say that i had a tough time online during the process of trying to get access to my spouse iPhone 12 pro max, i got scammed along the process so i needed two job now and that's how to get my funds back and also get access to my spouse mobile, It all ended well with the help of wizardhary AT programmer DOT net who i also whatsapp +1 (807-808) 6168, you can reach him today and have your funds recovered within 16 hours to 24 hours. 6/23/2021 09:34:28 am
Life is so funny all filled up with shackle's and storms by yet the Almighty bring forth a helper even when we don't deserve it, I had a court case with my ex and tried to hire a hacker to get me proof instead this hacker turn me down and run away with my money, after that I was referred to [email protected] who truly did what I asked, in no much time he also recovered my stolen funds, now I won the case and I'm living happily with my kids. All thanks to wizard Harry. we mostly talked on WhatsApp so it will be very fast to connect with him on WhatsApp +1-807-808-6168
recoverlife77
6/28/2021 10:28:43 am
wizard harry is a scam. he quote $2500 to help me recover funds with crypto currency and knew i was scammed out of my lifesavings but he kept asking for more and more. at the end i lost 11k to him and never recovered a dime. if you want to keep losing and being scammed then ask him for help. Now i am in more debt cause i kept borrowing and he kept asking more to purchase software. these reviews are written by him and dont trust.
grace
7/6/2021 06:34:36 pm
Clark James
7/10/2021 01:59:23 pm
I had credit scores of 504(transunion) 511(Equifax) in January. I applied for loan in March when I desperately needed to get a house for my wife and kids but was not approved because of my low FICO scores. Out of desperation i started looking for help and I came across a post about a professional hacker called RANSOM WARECREDIT I was so nervous at first thinking they would take money and disappear on me but at the same time i really needed help so I gave them a shot. They magically boosted my FICO score to 760 within 72 hours across all 3 credit bureaus and I was approved for the loan within a week. I still have my scores high because it is a permanent hack. I am so happy and thankful to them and i will recommend ONLY them to anyone in need of such services. CONTACT; [email protected] +1 (606) 715 6174.
Tricha Lopez
7/11/2021 11:52:32 pm
I`ve always taught online hackers were scammers and couldn’t improve a credit score until I met one on a discussion forum when I surf the internet on how to improve my credit score, I read a lady’s comment on how capable RANSOM WARECREDIT is of solving any problems that has to do with hacking. So I sent him a mail and asked if he could raise my credit score and also eliminate eviction off court records. Then he replied yes and asked me to provide him some info of mine he’ll need to run the hack. When I did just that, he completed the hack within 72 hours at a price that’s worth it. I give thanks to the ethical hacker for coming to my aid when I needed help the most. Reach the hacker at: [email protected] (606) 715-6174 and you’ll be amazed by his skills.
Temani Steve
7/15/2021 01:37:14 pm
I have always thought every company in the industry was a scam. Dianne a friend of mine had used Ransom Warecredit and told me that they did a great job. So, with caution, I contacted them and I was pleasantly surprised. They were very patient and set me up on a plan that was affordable for me. All in all I was very happy with their service and even more happy with my fantastic new credit score. I would recommend them to anyone looking for credit repair helps. ( [email protected] +1 (606) 715 6174 )
Darolett Guha
7/19/2021 05:21:49 pm
For the first time since the past 8 months I can sleep at night seeing light at the end of the tunnel for me and my family. I contacted RANSOM WARECREDIT 2weeks ago after months of worrying and sleepless nights, everyone who I spoke to or emailed has been fantastic especially Tricha a helpful polite kind staff who is a credit to the company, I’m still in the process of finalizing everything but I feel confident the outcome will be a good one. So I strongly recommend them to any one in sort of financial difficulties. ([email protected], +1 (606) 715-6174).
Kala Harry
7/22/2021 02:22:35 am
Awesome. I tried to buy a house only to be shut down because of credit history, which is completely paid for, and only happened cause we were struggling. We now have a good income and can’t buy a home.
Tim Harper
7/22/2021 05:25:46 pm
Are you still wondering how to repair your credit report? Aaron Swartz got you covered 100%. He removed all evictions, foreclosure, Tax liens, inquires, student loans, debts tax liens medical bills and raise my credit report to 800 excellent standard within few weeks. Contact him for your credit help AARONSWARTZCYBERSERVICES AT GMAIL DOT COM
Lorie Piek
7/25/2021 08:41:35 am
My husband and I were really unsure about contacting a credit repair company but I must say we had a great experience with Ransom Warecredit. Customer service went above and beyond to make sure we got the guidance and advice we needed to understand the process. They took my credit score from 502 to 786. They really know their stuff and were not pushy with their services. We highly recommend ([email protected] +1(606) 715-6174)
Wizarderrick
7/28/2021 06:26:51 pm
BITCOIN, BINARY OPTION: Please everyone should be careful and stop being fooled by all these brokers and account managers, they scammed me over $200,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, in the end, I lost all my money. All efforts to reach out to their customer support desk had declined, I found it very hard to move on. God so kind I followed a broadcast that teaches on how scammed victims can recover their fund, I contacted the email provided for consultation, I got feedback after some hours and I was asked to provide all legal details concerning my investment, I did exactly what they instructed me to do without delay, to my greatest surprise I was able to recover my money back including my profit which my capital generated. I said I will not hold this to myself but share it to the public so that all scammed victims can get their funds back, ::::::: if you have problems on any stuffed like a Recovering Scammed funds, recover your Lost bitcoin, Bitcoin mining, Flipping cash, Deleting criminal records, Clear Taxes, Increase your Credit score and top up balance, DMV database, Access your spouse/partner social media, Monitor your colleague and a lot more, Email: ( [email protected] ) I recommended Email: vitor(AT)programmer DOT net, for Funds Recovery/ Cryptocurrency/ Recovery of Stolen Bitcoin / Bitcoin Mining / Increase your Credit score/ MOBILE SPY REMOTE CONTROL ACCESS AUTHORIZATION. Removing Bad Records from Both Public and Private database: WhatsApp contact: (+1) 519 / 398 / 1460 My Regard I recommend professional expert Email: Vitor(AT)programmer DOT net, for Recovery Funds/ Cryptocurrency/ Recovery of Stolen Bitcoin / Bitcoin Mining/ Increase your Credit score/ MOBILE SPY REMOTE CONTROL ACCESS AUTHORIZATION. Removing Bad Records from Both Public and Private database: Whats App (+1) 519 / 398 / 1460
Diana Lloyd
8/6/2021 07:51:07 am
I got my credit report fixed last one month ago with the help of the credit lord named Aaron Swartz. He completed the hack within few weeks at a price thats worth it. He wiped all negatives items collections, inquiries and boosted my score to 780 respectively with no traces with some benefits such as business loan, high credit card limit and funded my bank account. I must let the word knows that these guy his good. CONTACT; [email protected] OR +1 (614) 344-8376
Francois
8/7/2021 07:08:16 am
Recovery Lost Funds From Online Scammer's/ Cryptocurrency/ Recovery of Stolen bitcoin / Bitcoin Mining/ Increase your Credit score/ MOBILE SPY REMOTECONTROL ACCESS AUTHORIZATION. Removing Bad Records from Both Public and Private database via Email: [email protected] and WhatsApp contact : +19895445367
Bitcoin Generator
8/9/2021 04:16:33 am
I DON'T BUY BITCOIN, I EARN IT DAILY FROM MY INVESTMENTS WITH A RELIABLE PLATFORM.
samuel bricks
8/9/2021 05:17:04 pm
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or 8/22/2021 09:13:32 am
I am open to share my experience with bitcoin investment and losing money to scammers. However, yes it is possible to recover your stolen bitcoins. I never believed in bitcoin recovery because I was made to understand that it was not possible. However, sometime in JumeI fell for a forex scam which promised overly high returns and I ended up losing close to $45,000. I searched for a month for help until I finally came across an article on reddit in regards to recovering stolen cryptocurrency so I reached out to them, albertgonzalezwizard (@) gmail com, I was so scared and skeptical because I have heard of bad experiences but I decided to give them a try and to my greatest surprise I was able to get all my stolen bitcoins recovered from the scammers within a very short time frame. If you are experience same problem simply contact him Whats App +31684181827 or Telegram: +31687920980 8/22/2021 11:56:15 pm
If you require professional help to recover your stolen cryptocurrency/Binary/Forex, forgot your password, sent BTC to wrong wallet address or hack your spouse’s phone remotely, spying on cheating spouse deleted chat conversation retrieval contact (vitorzprogrammer@Gmail com) WhatsApp +15193981460
Miles Caleb
8/24/2021 02:47:38 am
Hi guys, I want to share my experience with you, about 10 Months ago in a bid to repair my poor credit score of about 523, I came across a fake hacker who promised to help out, but ended up worsening my situation, I spent over $7,500 and nothing changed until Mrs. Terry a very close friend of mine introduced me to CYBER CREDIT GURU, a professional Hacker who changed My life tremendously. CYBER CREDIT GURU cleared all negative items from my profile and increased my score from 523 to 805 in less than 8days. I must confess, they are the best. If you are going through similar or worst situation than I did, you can reach out to them via CYBERCREDITGURU AT GMAIL DOT COM or call +1 (650) 239 7249.
Laura Roland
8/24/2021 07:55:47 am
Hello, everyone, my name is LAURA ROLAND am from the United State Of American I was in a sad relationship that always makes me feel loved and my boyfriend never take anything serious I told him I want to invest a huge amount of money in online investment and it turns out to be a rippers project company. I was so happy to see a testimonial given by someone called Maria James about his cheating ex-husband that wanted her father's money so I have to contact the email of the man that helps her out in exposing him, for him to help me and recover my lost funds to a wrong account with all pleasure he responds to me urgently and help me with the hacking of the account and I got my funds back he is best and good in his work contact him [email protected], contact him on WhatsApp with (+1- /807-23 ) 4-0428 ;) Immediately for your areas of Hacking services I have to share the Good news with everyone so u can be able to recover your lost funds, your Bitcoin, phone spy, and Instagram hacking, Facebook hacking, Snapchat hacking, twitter other services
Thomas Brian
8/27/2021 05:31:20 pm
Thanks to Jamie. i was able to recover all my lost bitcoin from forex tradingguys, when it comes to recovery of funds either from binary options, crypto, forex and ponzi schemes. ( [email protected] ) His the best recovery expert i have ever seen all my life. He recovered my funds and also funds of my friends, colleagues who were in similar situation as i was.
Kane
8/28/2021 07:30:35 am
I am open to share my experience in Bitcoin recovery and to also enlighten everyone on how I was able to recover my stolen bitcoins from scammers fronting as an ICO , feel free to reach out to the recovery company that helped me Instant Recovery at &*(instantrecovery12 #at# gmail dot com)*&
samuel bricks
8/29/2021 04:50:24 pm
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or
Mark lawrence
8/30/2021 05:15:30 am
How to recover Cryptocurrency ; Recovery from crypto wallet hackers, Binary Option & fake investments e.t.c Have you ever been a victim of a scam ? Have you lost your money to scam imposters online? I implore you to contact this trustworthy hacker and recovery expert [email protected] TO HELP 8/31/2021 07:25:22 am
Good day everyone reading . If you are seeking means to recover cryptocurrency , tokens, coins and funds lost to any form of online scams in binary options, forex crypto-trading and investment , do yourself a favor and contact Coinwalletrecoup . Com. This recoup company literally saved my life when they helped me recover tokens of over $233,000 from online rippers impersonating group admins on WeBull and Tradestation, my 12 phrase got compromised .They had my blockchain wallet ransacked it and I was left with nothing. I almost lost all hope till I read a review online about this company Coinwalletrecoup . Com that saved my life by helping me recover my stolen funds. I provided details of the incidence and necessary information to complete recovery program and under a week my coins and tokens were recovered by them. All thanks to COINWALLETRECOUP . COM . You Are the Best!!
BRUCE WAYNE
9/2/2021 03:07:04 am
I recently needed a private investigator or a hacker to help me pull one or two strings for the successful completion of my goal. Over the years I have came in contact with different types of scammers and users until I almost gave up then I heard of the name WHITEHATS- To my greatest surprise it came out that the WHITECOLLARS are all I have been searching for many years. Contact them for any hacking services for ease and fast delivery of any operation that involves a computer, other services like Phone Spy, Phone hack, Phone tracking, Credit boost up with all credit bureaus, Credit card top up, Bank Loading, Blank ATM cards, and many more. Mail- WhitehatspytechATcyberservicesDOTcom or WhitehatstechAtgmailDotcom, YOU WILL BE SURE TO THANK ME LATER
ellissa Rockwell
9/2/2021 04:33:04 am
EVERYONE AND ANYONE WHO HAS LOST THIER BÍŤČÕÍÑ OR FUND TO INVESTMENT ŠČÄM BÍŤČÕÍÑ MINING ŠČÄM, HACKED OR STOLEN BITCOIN SHOULD EMAIL FÅSTŘËČÕVËŘÝ02 HÃŤ GMÃÍĹ ČÕMË. HE IS A PROFESSIONAL ŘËČÕVËŘÝ EXPERT THAT SUCCESSFULLY ŘËČÕVËŘED 120K BÍŤČÕÍÑ I LOST TO INVESTMENT ŠČÄM.. YOU HAVE TO HIRE HIM HE IS JUST THE BEST. AND THE BEST PART IS THAT AS A GUARANTY THAT HE GETS THE JOB DONE, HE DOES NOT CHARGE A PENNY UNTIL AFTER THE JOB IS DONE.
Carl
9/3/2021 02:44:31 pm
I am open to share my experience with bitcoin investment and losing money to scammers. However, yes it is possible to recover your stolen bitcoins. I never believed in bitcoin recovery because I was made to understand that it was not possible. However, sometime in October I fell for a forex scam which promised overly high returns and I ended up losing close to $55,000. I searched for a month for help until I finally came across an article on reddit in regards to recovering stolen cryptocurrency so I reached out to them, INSTANTRECOVERY12 GMAIL dot com. I was so scared and skeptical because I have heard of bad experiences but I decided to give them a try and to my greatest surprise I was able to get all my stolen bitcoins recovered from the scammers within a very short time frame. I don’t know if I’m allowed to share the links on here but you can contact if you also need help, all you have to do is send them a text via their mail above
Renee Collins
9/6/2021 04:32:27 pm
Yes it is possible to retrieve your stolen bitcoins. I never believed in bitcoin recovery because I was made to understand that it is not possible. But sometime in February I fell for a binary options scam which promised a higher return and I lost close to $75,000. I read an article on (reddit) as regards to a recovery expert and genius so I reached out to (KONTACTTHEALIENDELTA @ GMAIL DOT COM), and to my surprise I got all bitcoins recovered within 42hours frame. I don’t know if I’m allowed to share the links on here but you can contact him if you are finding it very difficult to withdraw your funds at, (KONTACTTHEALIENDELTA @ GMAIL DOT COM)…… All Thanks To Them
Jason Thomas
9/6/2021 04:35:30 pm
I had a fake telegram group admin contact me and gave me a phishing link in which my 12 recovery phrase were compromised. These evil persons gained access to my crypto-wallet and stole all my coins and tokens worth over $230,000 . I was in great despair due to this situation, I was confused till a group member on the telegram referred me to (KONTACTTHEALIENDELTA @ GMAIL DOT COM) .This recovery agent is really God sent. After relating all of my predicaments, details of incidence and necessary requirements for my recovery program , it took them less than a week to track and recover all of my tokens and coins back, they helped me hack the perpetrators wallet and all of my coins were returned to me . I am so amazed , joyous and appreciative . I don't know what I would do without this specialist. They specialize in chargeback disputes and their team knows how to identify these types of scams. If you invested in Crypto and believe you have been scammed, contact their experts today and they will help you recover your losses. Contact : (KONTACTTHEALIENDELTA @ GMAIL DOT COM)
Chris Walker
9/7/2021 09:23:58 am
Hello, I came to CREDIT FIXER NETWORK for help because I’m buying my dream home this year and I wanted my credit to be great before I purchased. So far, it’s been great, in just less than 6days.I received an email stating that changes has been made on my credit profile. I checked my scores and my Experian went up 120points, Transunion-110points, and Equifax 130points. This is just the beginning and I’m already seeing more good results. He cleared all collections, bank judgment, debts, medical bills and late payments. I would definitely recommend [email protected] to anyone who is looking to get their credit in order.
James nash
9/9/2021 03:55:39 am
I'm a tech pro a programmer and a IT analyst with Amazon for 7 years before I become an independent cyber investigator. so I can tell you expert are all over & skillful differently . hire me for all kinds of funds tracking, investigation and recovery procedure. I don't work with any website firm or recovery organization,if you ask me why? reason is government don't & will never license a hacking tech firm cause hacking is a act punishable by law they, so many create website & they ask for UPFRONT PAYMENT as means to look legit and still swindle people of there hard earn. I work independently and in affiliation with experts in the government secret services successfully I've recovered over $45 thousand worth of Bitcoin. I'm available 24/7 on BINARYEXPERTRECOVERY07 @ GMAIL . COM
Sarah Bolin
9/9/2021 07:49:09 am
Yea , I got everything already set up within same day I contacted them I guess it was really a serious work day for them
Sharon Riddle
9/13/2021 09:21:31 am
I strongly recommend the service of a GREAT proffersional recovery expert to you and his email is [email protected].
Susan Job
9/19/2021 09:18:05 am
I'm using this opportunity to recommend and show my gratitude to this professional hacker called [[email protected]] after being scammed by fakes in trying to hack my so called cheat of a husband, we were going through hard times almost before our divorce and my husband was always insecure and jealous, the hacker helped me hacked my husband details and i was able to clone his phone successfully, granting me unlimited access to his mails, Whatsapp and Facebook messenger, getting messages from 6 months past and even deleted some messages and mails, i was able to gather all the information and messages I needed.
Maeve
9/23/2021 02:26:09 pm
I broke down for weeks after loosing a huge amount of money to blue trading. All efforts to get back my money turned out useless, until I encountered INSTANTRECOVERY12 (([AT}]) gmail .com who helped me recovered my funds without down payment.
Very interesting Topic. Many articles I come across these days do not really provide anything that attracts others as yours, but believe me the way you interact is literally awesome I do respect that so much. I will instantly grab your rss feed to stay informed of any updates you make and as well take the advantage to share some latest information about
RICHARD
9/28/2021 10:52:52 pm
Do you need a hacker? Do you need to keep an eye on your spouse by gaining access to their emails? As a parent,if you want to know what your kids do on a daily basis on social networks (This includes facebook, twitter ,instagram, whatsapp, WeChat and others to make sure they’re not getting into trouble? Whatever it is,Ranging from Bank Jobs, Flipping cash, Criminal records, DMV, Taxes, Name it,he will get the job done.He’s a professional hacker with 20 Years+ experience.Email him on [email protected] for him to get your work done ... Tell him Richard referred you okay.
George Orwell
9/29/2021 05:59:00 am
So, I’ve been getting “credit offers” in the mail (I don’t live there anymore so I haven’t seen what they are exactly). My mom was scared my identity was stolen because I tried to fix my credit sometime ago and for some reasons I had to back out. My score decreased to low 500 and after I came across Ace Cyber Group on a blog and decided to fix my credit with him, you will be shocked with the result. Ace also erased the credit card debts, student loans and repos from my credit. Just two weeks after I started working with him, I decided to check my report, I have a mind-blowing FICO score of 790 and those items have been erased completely and he said they will never come back anymore. I’m sure you will be glad to reach out to him via WhatsApp: (925) 238-2217 or email ACECYBERGROUP AT GMAIL DOT COM.
Chris job
10/3/2021 04:47:08 am
I am a father of 4 children and I have always wanted to buy my dream house. but by credit report, I have never been able to. My score was 475 due to medical bills, student loans, etc. well I trusted [email protected] with my credit and he delivered my life from shame and failure bringing joy and reason to be happy again. He raised my score to 790 and deleted all the bad items on my report and it still looks nice up to date.
Haily Bradwell
10/4/2021 09:43:23 am
HAVE YOU LOST YOUR MONEY TO BINARY OPTION SCAM OR ANY ONLINE SCAM WHATSOEVER?.DO YOUR DESIRE CREDIT REPAIR[EQUIFAX, EXPERIAN, TRANSUNION? WELL, YOU HAVE FOUND REDEMPTION IN ASORE CORP.
cyber lender
10/6/2021 09:46:42 am
Need emergency funds? Apply now and get your cash approval. we offer the following financial services:
lucy kelvin
10/13/2021 05:33:29 am
Having my credit scores boosted in less than 72hrs without any traces being found on my report is the best thing that has ever happened to me! A colleague of mine got her credit scores increased by him which she introduced me to. He was able to raise my credit score to high 820 and clear off my credit card debts and also added some trade lines. CONTACT; thecredittreatment @ gmail dot com
Holly Wolff
10/14/2021 08:09:38 pm
First of all you have to note that not all of those out there who pose to be hackers are real and from my experience, this job doesn’t come so cheap. In a process of trying to get my credit repaired I fell into a fake person who worsened my problem, as I was unable to refinanced my home due to my bad credit report that gave me a concern, I had to send my family to stay with my sister, while I look for solution to my problem. I had late payment bankruptcy student loans tax liens some collections, 3 closed accounts, he took over $9,000 in bits this happened until I met this Private Credit Repair Company called 760PLUS CREDIT SCORE A friend read about them on CK and informed me, I contacted them after reading some testimonies about them, they ran my credit report, analyzed the credit score and determined which action will have the greatest impact. They raised my credit score to 802 and Wiped off all negative items on my credit report, within 12days. They made it work with a stress free process and I have a clean profile now. My heart is full of gratitude. If you want to reach them write 760pluscreditscore At gmail Dot com / 304 774 5902 they’re truly the best you can ever work with.
Cynthia Norton
10/18/2021 08:52:25 am
Unbelievable! Aaron Swartz is still the best credit doctor, I had a Chase credit card debt which low credit score with a lot of negative items collection which was listed on my credit profile. He help me removed the negative items on my credit profile and raise my credit score to 825 within few days. Paid off my credit card debt and transfer some fund to my bank account , He actually kept to his word. You can also reach him for help CONTACT address ; [email protected] OR +1 (614) 344-8376
jason
10/18/2021 03:48:30 pm
I was twice a victim of a cryptocurrency scam lead by romance trying to find the right partner.I needed my credit cleaned so I can get a place to live with my family. I had repos, late payments, bankruptcy, judgments was filed and I needed someone to help me without scamming me because it was my family I wanted the housing for. I decided to narrow my search to a trusted credit site , luckily for me, I found several good reviews on ARON LUCS a trusted credit repair specialist. I contacted him on;[email protected] +1(210) 646-1791 and after discussing the process, we got started. He raised my score from 456 to 760 , posted good tradelines on my report, deleted the bankruptcy and the judgments and increased my credit line to $60k. All late payments appeared as on time payment and he effected the changes across all 3 credit bureaus. His job is legit and untraceable.I can’t thank him enough and I knew i owe him this
Aron Lucs
10/20/2021 05:15:53 am
I was twice a victim of a cryptocurrency scam lead by romance trying to find the right partner.I needed my credit cleaned so I can get a place to live with my family. I had repos, late payments, bankruptcy, judgments was filed and I needed someone to help me without scamming me because it was my family I wanted the housing for.such as hacking emails, Facebook, Twitter, Instagram, note changes, deleting criminal records, credit and debit refill, reloading insurance documents, lost or lost file recovery, background check . I decided to narrow my search to a trusted credit site , luckily for me, I found several good reviews on ARON LUCS a trusted credit repair specialist. I contacted him on;ARONLUCSHACKCOMPANY AT GMAIL.COM wHATTS APP +19014683874 and after discussing the process, we got started. He raised my score from 456 to 760 , posted good tradelines on my report, deleted the bankruptcy and the judgments and increased my credit line to $60k. All late payments appeared as on time payment and he effected the changes across all 3 credit bureaus. His job is legit and untraceable.I can’t thank him enough and I knew i owe him this.
Clara smith
10/20/2021 04:22:16 pm
My husband and I had some couple of negative items with low score that disqualified us from everything. So we searched for a credit expert on a review to help us fix our credit profile and we agreed to trust [[email protected]] After we have read good reviews and trusted recommendations from people about him, we explained they negative items on our reports and he gave us a period of one week. Eventually, we finally got an excellent result within 7 days. Our score was boosted from 480 to 850 respectively. All debt were marked as paid, late payment appeared as on time payment and other negative item were deleted. I strongly recommend his good work.
Susan Job
10/26/2021 10:05:48 am
I'm here to testify about Blank ATM CARDS which can withdraw money from any ATM machines around the world.. firstly I thought it was scam until I saw so many testimony about how [email protected] sent them the blank ATM card and how it was used to withdraw money in any ATM machine. So I decided to give it a try I contacted him and applied for the Blank ATM Card. To my greatest surprise I got mine last week and i have used it to withdraw about $10,000 for free. CYBER LOAN AND COIN RECOVERY is giving out the card just to help people even if it is illegal but it helps a lot and no one ever gets caught or traced.
Tracy Smith
10/27/2021 10:55:00 am
Jennifer brown
10/27/2021 05:15:21 pm
I just can't stop sharing the Gospel of my new Hacker friend until other people enjoy his amazing service. He's one of a kind. He hacks anything and everything. At first, he didn't want to work for me because he considered the job too low for him. I had to make him understand that there are lots of people out there like me who really My are jennifer Roland need his help in getting accounts, websites and phones hacked. He called his method of hacking "specter mode". I was curious so I asked him what it meant and he made me understand that his hack is untraceable and unnoticeable. He is tested and trusted, and a Guru when it comes to hacking. Services include *Cloning* Tracking* Spying* Retrieving of deleted text messages* Upgrading of results etc. All at an affordable fee. You can contact him via [email protected] and are whatsapp number +[807]700.3319 It was the best experience I have ever seen in my life. He is safe and secure. And he gets your job done in less than 4 HOURS. He also offered me a 24 hour refund if I find his service unsatisfactory.
Roger J. Curnutt
10/28/2021 03:44:45 am
Once your virtual currency has been stolen it is incredibly unlikely that you will be able to recover it. In theory, it’s possible to track your stolen bitcoin by monitoring the blockchain – in practice, however, this is made difficult by both the anonymous nature of the currency and the fact that the thief will most likely use a bitcoin exchange to trade the currency for normal cash straight away. However, money does leave a trail and you may be able to follow it to the identity of the criminal. Even if you successfully use public ledgers to trace the currency, since most cryptocurrency is decentralized there aren’t many routes you can follow to get it back. Know more about recovery at primedefenders dotorg 10/29/2021 06:20:18 pm
I would strongly love to recommend the services of the best team of dark web hackers. They are professional and very discreet in carrying out their jobs, they have the best customer service agents and satisfaction at heart. If you have any services you wish to contact them for, go on albertgonzalezwizard (@) gmail com / Whatsapp +31684181827 or Telegram: +31687920980. They help track and monitor your cheating partner's phone without his idea, clear or erase criminal records as well as repair a bad credit score, all social media hacks,funds recovery and many others.
Jennifer brown
10/31/2021 11:13:26 am
I DEPOSITED BITCOIN IN A TRADING WEBSITE ,THEN I WANTED TO SELL AND WITHDRAW MY FUNDS AND PROFIT FROM THEM, I HAVE MAILED AND MESSAGED THEM, BUT NO RESPONSE.. I SEARCH FOR HELP, GOT SCAM BY ONE RECOVERY COMPANY, WAS SO SAD... THEN I CAME ACCCROS A REVIEW THAT TALKED ABOUT [wizardwilsonsoftware (@) Yahoo.com[]... I SIGNED UP AND OPENED A CASE.. I WAS ASSIGNED MR ANDRE, WHO HAS BEEN HELPING ME, SO FAR I GOT MY INITIAL DEPOSIT BACK... AND STILL WORKING TO GET MY EXPECTED PROFITS BACK.... SEND A DETAILED MAIL AND OPEN A CASE WITH [wizardwilsonsoftware (@) Yahoo.com his whatsapp number (+1) 807,700,3319] - OR SEND A DETAILED MAIL OF THE SCAM ORDEAL TO wizard wilson software [THEY SPECIALISE IN DEALING WITH ONLINE SCAM AND HELP PROVIDE REIMBURSEMENT TO THEIR VICTIMS USING DISPUTE, TRACKING DOWN DIGITAL FINGERPRINTS, CYBER ANALYSIS AND THOROUGH INVESTIGATION wizardwilsonsoftware (@) Yahoo.com his whatsapp number (+1) 807,700,3319
CHARLIER MCCOY
10/31/2021 12:21:08 pm
BITCOIN RECOVERY/BOOSTING MADE EASY.
Paul moore
11/1/2021 05:11:10 am
If You Are Trying To Catch Your Cheating Spouse In The Act, I Strongly Recommend You Contact This Awesome Hacker That Helped Me Monitor My Husband’s Phone When I Was Gathering Evidence During The Divorce. I Got Virtually Every Information She Has Been Hiding Over The Months Easily On My Own Phone: The Spy App Diverted All Her Whatsapp, Facebook, Text Messages, Sent And Received Through The Phone: I Also Got Her Phone Calls And Deleted Messages. She Could Not Believe Her Eyes When She Saw The Evidence Because She Had No Idea She Was Hacked, I Didn’t Need To Touch Her Phone At all,.I Certainly Recommend whatsApp him +1(289)960-0524 or Email him [email protected]
Linda Jackson
11/2/2021 03:58:21 am
All thanks to Trovian Credit Repair for bringing me out of shame, I am a mother of four kids; I lost my husband 4years back. he left I and my kids with lot of debts and evictions, the little business I manage to feed my family got crashed due to the pandemic, I call my sister to ask if she had any idea about who can fix my credit report, she introduce me to Trovian Credit Repair, I contacted them via; [email protected] OR +15059263648 they did a great job on my credit report, they cleared all the bad items of my report and raise my credit score to 810 and also give me a good credit limit, am glad to testify of your good job Trovians. You can contact them via the above mail or text
KEL CHAMBERS
11/3/2021 01:47:41 am
BARNESHACK INTEL is a Group of Multinational Hackers. An affiliate of Evil Corp. We make sure by all means necessary that our clients get the best of services on A PAYMENT AFTER JOB IS DONE BASIS. Rather than send money and trust Someone to fulfill your deal, you can make sure the job is done before WORKMANSHIP is paid. Excellent Customer Service AND A 100% Guarantee.
Jenna Walter
11/4/2021 02:01:50 pm
Each time I call my husband office they keep telling me my husband has a 3pm appointment and this has been happing for a while now, am always worried about my husband leaving the office by 8pm yet he won’t open up to me about the contract he has been trying to seal, then I hired ''(wizardjackson (@) yahoo dot com)'' to make the investigation for me without any notice, I got access to my husband phone remotely after going through his text messages and all I found out that there is a lady my husband always see by 3pm then I went further because ''(wizardjackson (@) yahoo dot com)'' also provided me with my husband deleted messages and I saw that my husband makes love to this lady every day and when he comes home he starve me from sex but am so thankful to ''([email protected])'' and his wathsapp number (+1) 807--234- 0335) for the best services he rendered to me.
Collins Smith
11/5/2021 08:59:34 am
I lost my coin to fake Binary Options trading impostors on Facebook, they contacted me as blockchain official support and i fell stupidly for their mischievous act, this made them gain access into my blockchain wallet whereby 7.0938 bitcoin was stolen from my wallet in total. I was almost in a comma and dumbfounded because this was all my savings. Then I made a research online and found a recovery expert , with the contact address [email protected] I wrote directly to the specialist explaining my loss founds. After 24hours all my lost founds was recovered back to my wallet. all thanks to him and his service.
Ron Howard
11/5/2021 02:02:49 pm
Hello everyone my name is Ron Howard my problem started eight months ago when my wife illness became unbearable, I spent all my savings on hospital bills and also went beyond my credit to make her feel better, after that I notice I have a lot of debt which I need to clear of my credit report while thinking on how to resolve this issue, a friend of mine introduce me to HACKNET CREDIT SPECIALIST he helped me cleared the debt including the collections items, Tax Liens late payments, personal loans and also raise my credit score to 799plus across all bureaus. Hit him up for credit solutions, [email protected]. He’s one hundred percent legit and trusted.
Emilie Winfrey
11/5/2021 06:21:10 pm
Hello everyone I can proudly tell you that indeed 760PLUS Team currently has the solution to any kind of credit problem they have proven beyond doubt to be second to none in terms of topnotch credit Fix services. My score was just raised to satisfactory and I have been watching it for some days now due to my skeptic nature but it’s been perfect, they did some mind-blowing works on my profile that I think enumerating them on this public forum wouldn’t be necessary. They are just the best and always get job done, it’s safe with [email protected] /WhatsApp +1 (626) 514-0620. Permanent score assured.
Julie Greene
11/8/2021 06:00:49 am
I was looking for a good way to repair my credit card, Finally encountered with fake hackers. trust became very difficult for me because of their inability to clean up the financial mess on my credit report. I was researching on a blog and came across good recommendations about [email protected] I decided to give a try. I text and explained to him the bad debts on my profile. surprisingly after 14 days I got a text that my credit score has being increased from 420 to 810, He also taught me how to maintain my financial position to be on good credit line. I recommend this professional and trusted hacker today for the amazing work he did for me
Pagesteve
11/14/2021 07:14:21 am
This is my advice to anyone who wants to hack a phone, make sure you pay for the right hacker like Fred. I wish I knew this sooner, I would not have spent so much on different spy apps. It took sometime before I finally found a way to hack my wife’s phone without having access to it. I mentioned my fears and insecurities to a friend and she recommended this guy to me: Fred hacker, This guy provided a service that allows me to monitor her calls and conversations. I haven’t decided on what to do yet. I don’t think I can continue in this marriage. She is cheating on me contact him via [email protected] whatsapp +1(289)960-0524) Cheers Doom hack
George
11/17/2021 02:53:03 am
How to recover funds / crypto currency ; Binary Option & fake investments RECOVERY Have you ever been a victim of a scam? Have you lost your money to scam imposters online? I implore you to contact this trustworthy recovery expert Secure2invest.com TO HELP RECOVER ALL YOU HAVE LOST, I was a victim of fake people posing as binary options and bitcoin investors, I lost a sum of $4,000 and 2BTC from my bitcoin wallet to these fakes. It took a while before I realized they were scams and this really hurt . Then an in-law of mine heard the incident and recommended to me a specialist with the address - Secure2invest.com . They helped me recover my stolen bitcoins after providing necessary informations and program requirements and in less than 5working days the fakes were caught and made to pay for what they did to me .if you have lost any amount to online scams and you're seeking to recover LOST FUNDS from wallet hackers, fake hackers, online dating scams, BTC wallet hack, recovery of lost funds from fake binary investors .Reach out to Secure2invest.com to help you ,and you will be so glad you did so, best believe .
Brian
11/19/2021 10:39:17 pm
paul
11/20/2021 03:10:33 pm
Catherine Goodwin
11/21/2021 06:34:13 am
Aaron Swartz change my life for good ever since he help me repair my credit report. He got all negative items removed from my credit profile within a week and including paying off my debts. He also raised my credit scores back to 845 excellent standard which reflect in all credit bureaus report without no traces. CONTACT address ; [email protected] OR +1 (614) 344-8376 I bet you to get in touch with him and thank me later.
james SMITH
11/24/2021 01:48:26 am
Are you in need of a private investigator in any area of your life??? then you can contact; services like; -spy into your cheating partner's phone(whatsapp,bbm.gmail,icloud,facebook, twitter,snap chat and others) -Sales of Blank ATM cards. -hack into email accounts and trace email location -all social media accounts, -school database to clear or change grades, -Retrieval of lost file/documents -DUIs -company records and systems, -Bank accounts,Paypal accounts -Credit cards hacker -Credit score hack -Monitor any phone and email address -Websites hacking, pentesting. -IP addresses and people tracking. -Hacking courses and classes CONTACT THEM= [email protected] you could also text +1 410 635 0697 text/ whatsapp and telegram their services are the best on the market and 100% security and discreet work is guaranteed
Ann Collins
11/25/2021 02:24:55 pm
The Year is almost running to an end and if you're still battling with your bad credit scores and other negative report on your scorers, I'll advice you don't start a New Year with that! GARY MCKINNON is always there to help you raise your credit score to excellent, erase all negative report and pay all debt. contact him right away via email [email protected]
Gail Duncan
12/2/2021 11:04:18 pm
Gary Mckinnon is here to help you with all your difficulties regarding with your bad credit scores , bitcoin wallets, negative reports and also your debts with all excellent. He is very reliable and good at this work!! Y'all in need should get in touch with him right away. I wish you all best of luck and season greetings! Contact him [email protected]
Nathaniel Caldwell
12/6/2021 02:44:39 pm
It’s 100% possible to fixed your credit report with the help of Aaron Swartz credit guru. CONTACT address ; [email protected] OR +1 (614) 344-8376. He helped me hacked into the 3 credit bureaus and He help me raise my FICO score to 785 and Help me pay off my debts, also delete all negative items on my credit report. He’s capable of Capable of hacking iPhone , android , WhatsApp, Twitter, Instagram, Bitcoin wallet, Facebook, Credit cards
Penny Creelman
12/8/2021 06:41:17 am
With the help of only one person, Gary McKinnon, you can fix all types of credit score concerns, restore your bitcoin wallet, and increase your scores to excellent in just 72 hours!!! [email protected] is the email address he can be reached at.
Leo Marcos
12/11/2021 11:03:33 am
Hello Friends, My name is Leo Marcos I live Colorado with my family. I'm a Truck driver and am always busy on the road. I want to appreciate TROVIAN CREDIT REPAIR for their monumental help recently on my bad credit I got to tell you this. My score was 510 I wanted to buy a house but I knew my credit was not up to standard to get a home. So I made a personal research along which i came across a review about TROVIAN on how they fixed a Man's credit and increased his score so I contacted them immediately they deleted my old accounts and increased my score to 803 which i was so surprised now I’m able to buy a house. I really appreciate their good work and i promised about telling everyone out there what they did on my report. They are very good and understanding expert you can easily reach them on [email protected] +1 (424) 307 4562
Sarah O’Brian
12/12/2021 09:08:52 am
Hello ! My name is Sarah O’Brian, I am a chartered accountant and mother of four from Michigan. Some time ago I decided to invest in cryptocurrency. I invested exactly $102,000 for a start with this fake broker www.24xforex.com and was made to believe that my investment had grown from my initial deposit of $102,000 to $250,700.This felt so good as the investment grew rapidly in just a few weeks. When it was time to take my profit, my withdrawal request was denied. Later on after much vain efforts,i realized that I might never get my money back.
Danny Cody
12/19/2021 04:27:21 am
Most times when i see people complain of what they go through due to their bad credit profile I will sit back and give thanks to TROVIAN, have been going through a bad report those days and I totally understood how bad the situations was and on bearable for me to get my own apartment and bank also denied me access on getting a credit card, my best wasn’t working until i came across TROVIAN CREDIT REPAIR and he helped me erase all the bad items he also helped me get a credit card have been aspiring for a long time also raise my score to 810. Now am in my own apartment am so happy. You can reach him if you want to fix your credit report through his email [email protected] TEXT +1(424) 307 4562
Elena Hicks
12/19/2021 11:54:47 am
Are you tired of fixing your credit report, Aaron Swartz got you 100%. He’s affordable and swift response. He help me raise my FICO score to 785, all my negative items were deleted and medical bills was removed permanent. I have purchased my dream Mansion and I’m free to apply for anything i wish. CONTACT address ; [email protected]
Debbie Jefferson
12/23/2021 04:13:30 pm
I never believe i could ever own a mine store here in California after been through a lot of natural disaster which hurt my credit score so much until this great hacker name TROVIAN CREDIT REPAIR they really assisted me in getting my eviction off my credit report and raised my credit score back to 800 I am able to get my first mortgage loan been approved within few days and they added more trade lines to my credit report. Contact them through [email protected] +1(424) 307 4562
Matt Bergin
12/30/2021 01:56:53 am
For the last few months, applying for a loan has been really tough for me since I wanted to purchase a house and do other things, but I have been refused multiple times due to my poor credit ratings. I had lost hope until I came across Gary Mckinnon. I described my predicament to him, and he was able to help me improve my credit ratings to excellent levels. Do you have the same or a similar problem? I recommend you contact him right away at [email protected]
larry
12/31/2021 03:37:34 am
Hello friends, I’m from London and I’m using this medium to testify to the genuine work of an Hack Pro and PIA.When it comes to hacking although, I never believed it could be possible for me to access someone device without touching it but after contacting the hack pro ([email protected]), now I know better.They hack all social media platforms, smartphones, bank Accounts, help recover stolen crypto and even more.
MICHELLE MCCAULEY
1/1/2022 02:31:36 pm
Never met any hacker as discreet and fast like this WHITECOLLAR Hacker. He’s called WHITE and he has helped me in multiple ways first was when my ex wife cheated on me and now he’s helping me paying my credit cards debts plus he helped me gain access to my spouse phone remotely and I was able to use that against him in court. I must say he’s the best at what he do and I recommend him to the world. Email; WhitehatstechATgmailDOTcom , you can be sure to thank me later. I will keep on telling the world that he’s the best out there, I am very thankful because he gave me and my kids a second chance
Joey
1/9/2022 06:54:57 am
I was so ripped off on binary options while trying to get my life savings multiplied. I was confused on what I could do to get my money back because I already read online that going to a lawyer or any chargeback company wouldn't help. After so many research and help requests from friends, I later after a while luckily bumped into a website "HACKSANDRECOVERY DOT NET" in the process of my online research, I went through the website and saw they help recover funds from binary options scam, cryptocurrency scam, etc. I took the risk and contacted the website's admin, I explained the whole situation to him, how the investment went and the binary options brokers I dealt with. He assured me that I would get my money back but it would take just little time. He requested for all the details about the brokers that scammed me and also about the amount I invested, I provided all and kept hoping on God. Luckily for me after some time, he was able to recover nearly 85% of my lost funds into my local bank account I provided to him, I was highly amazed because I felt all was lost already. I advise you visit the website "HACKSANDRECOVERY DOT NET" now also if you need to recover your funds from any scam broker
CONTACT:
Antony Austine
1/9/2022 04:09:19 pm
Lexington Law is a huge rip-off scam. They tell you that they will fix your credit; they make big promises to get you to sign their contract. You pay the monthly due as instructed and get nothing in return. I used them for about a year and my credit scores rate went down. I had a very sick child and had a lot of medical collections and hard inquiries. I was young and dumb back then. I got across TROVIAN CREDIT REPAIR they are genius, get through with them today and you will be glad you did. [email protected] OR CALL +1 (424) 307 4562 He saved me from Financial ruins and bankruptcy...they deleted all the hard inquiries ,collections, derogatory on my credit report and then proceeded to improving my credit score to 800's
Bill Skinner
1/10/2022 10:42:44 pm
Chelsea Tompson
1/13/2022 04:08:27 pm
I am glad to introduce you to TROVIAN CREDIT REPAIR whom services are 100% real and genuine; they help me fix my credit, paid all my debts, removed all collections and increase my credit card all within one week. I never believed this could be done but they proved me wrong by providing a good result which made me and my family happy....We are forever grateful to them for the good works, they pulled me out of hardship, but now we can get everything we want (Loans, Credit card, getting approved for higher limit).Reach out to them to get your credit fixed right now [email protected] or text them on +1 (424) 307 4562 to avoid been scammed by all the fake credit repair agencies.
ford williams
1/14/2022 05:36:22 am
I just have to introduce this hacker that I have been working with him on getting my credit score been boosted across the Equifax, TransUnion and Experian report. He made a lot of good changes on my credit report by erasing all the past eviction, bad collections and DUI off my credit report history and also increased my FICO score above 876 across my three credit bureaus report you can contatc him for all kind of hacks . Email him here via Email him here via [email protected] or whatsapp Number: +1 410 635 0697.
Stacey Willie
1/17/2022 07:30:23 am
I found several good reviews about ADRIAN LAMO, A trusted credit repair professional. I contacted him and after discussing with him, we got started. He raised my score from 420 to 840 across all 3 credit bureaus, posted good trade-lines on my report, deleted my bad records and increased my credit line to $70k. He cleared all my bank account and credit card debt without traces. His job is legit and untraceable, You can get in touch with him via mail [email protected] or via text (413) 551-2034
Nancy Saroski
1/19/2022 10:37:43 am
I strongly recommend the service of a GREAT Hacker to you and his email is [email protected]. I have used him quite a number of times and he has never disappointed me.
John Brokers
1/19/2022 03:02:28 pm
I opened my first credit card 8 years back with capital one. I was advised to use it a lot and pay it off before due time. After some years I lost my job and I was on able to meet up, which affected my report. I had some credit debts, utility bills, inquires and some collective items on my report. I came across a review on the YouTube about a credit expert company called TROVIAN CREDIT REPAIR which got my attention. I contacted them, we settled with a price then they start working on my credit, in less than 7 days I received a message that some changes as been done on my report. They cleared everything and pay off my debts and also raised my credit to 799 from the initial 580. Mail them with the following [email protected] PHONE +1 (424) 307 4562. They are 100% legit.
John Brokers
1/20/2022 04:53:23 am
I opened my first credit card 8 years back with capital one. I was advised to use it a lot and pay it off before due time. After some years I lost my job and I was on able to meet up, which affected my report. I had some credit debts, utility bills, inquires and some collective items on my report. I came across a review on the YouTube about a credit expert company called TROVIAN CREDIT REPAIR which got my attention. I contacted them, we settled with a price then they start working on my credit, in less than 7 days I received a message that some changes as been done on my report. They cleared everything and pay off my debts and also raised my credit to 799 from the initial 580. Mail them with the following [email protected] PHONE +1 (424) 307 4562. They are 100% legit.
David Grants
1/23/2022 04:39:23 am
After filing for bankruptcy in 2021 , my life became miserable as I could not get approved for a loan anymore , I came across this professional credit repair expert who specializes in improving peoples credit ratings so I decided to give him a try. He increased my score to 810 on all 3 bureaus and permanently removed all the bad accounts I had on my report. All thanks to this dude called credithacker247 @ gmail..com, He is 100% reliable and genuine
Sharon Barnett
1/23/2022 03:05:22 pm
I have been with a cheating spouse before and trust me I know how it feels, those suspicions are not mere paranoia. If you suspect that he is cheating, he definitely is..I hired a PI who helped me install monitoring bugs on his phone that diverted all his messages( facebook, whatsapp, text messages, and even phone calls) to my phone (adriancyberghost@ gmail .com) is the man for the job with a very high level of professionalism, honest and highly reliable. I really enjoyed working with him and the few friends I told have been nothing but thankful to me for the referral.
Chris Taylors
1/24/2022 04:35:52 pm
When I suggest about buying our first home, my wife thought i wasn’t serious because we had a bad credit and couldn't get a loan with that but i was determined to get us out of our place to a better place and that was how the search on how to fix our credit started, luckily for me i stumbled upon this credible hackers TROVIAN CREDIT REPAIR. Words can’t express how good these hackers are. I mean they raised our scores and fixed our credit so we could apply for the loan. My wife trusts my intelligence and determination now. Here is what you need to reach them [email protected] OR TEXT +1 (424) 307 4562. I'm so proud to be writing this.
Benjamin Gross
1/28/2022 07:03:49 am
I want to sincerely thank Aaron Swartz for helping me to rebuild my credit report back to excellent within few days. My credit scores are around 549 for the 3 bureau's and I have some collections, a charge-off, some hard inquiries. He help me raise my FICO score to 825 excellent standard and Remove all negative items on my credit report, pay off my credit card debts. I am the happiest man on earth right now all thanks to [email protected]
Mercy Lawson
1/28/2022 08:17:51 am
I must say this is the fastest way to rebuild your credit score through this reliable special company TROVIAN CREDIT REPAIR I got divorced 5 years ago and it has been terrifying ever since. My ex let our house be foreclosed after I moved out, I had a credit score of 580, earn $80k and more than $3,000 in debt. I needed to get approved for a home loan in Texas. But I was turned down by a lot of companies due to poor credit. Then I got referred to [email protected] OR PHONE +1 (424) 307 4562 by a realtor. I saved their contact and mailed them for score increase .After making payments for the job my credit was cleaned and my score was increase to 799plus in less than 7days. This filled me with so much joy. I wish I contacted them earlier I wouldn’t have suffered to restore my credit. Quickly contact them on the above details if you require your credit fix.
Rich Pablo
2/4/2022 06:07:00 pm
Wow!!! This Is wonderfully Brought To Pass, they made it happen by turning my tears to joy with their help i was able to acquire a Home Equity and they also helped me pay off my credit card debt and raise my wife’s credit score to 809 excellently. They are professional Hackers. I can't just stop thanking them for their great job which i can never forget. They deal with all Other Related Services!!! Like removing of bankruptcy, criminal background and so much more kindly Contact them on now if you have issues relating to your report: [email protected] you can also call +1 (424) 307 4562. Thanks and remain bless.
Cassandra Nichols
2/6/2022 04:35:45 am
My appreciation gratitude goes out to Aaron Swartz, Aaron Swartz did what is impossible to fixed. He wiped all negative items collections and raised my score to 794 and I get to apply for loans and also to purchase a car without any issues. He also added a seasoned line of credit for me and I’m living happily with my family. You can hit him up on [email protected]
Janet Wayne
2/12/2022 09:24:25 pm
With the help of GARY MCKINNON, you can improve your credit ratings and restore your Bitcoin wallet in as little as 48 hours. He assisted me with mine, and he can assist you with yours as well. He's incredibly dependable, so contact him at [email protected]
Elizabeth Brooklyn
2/13/2022 04:38:26 am
GET RICH WITH BLANK ATM CARD ... Whatsapp: +18033921735
Lauren Carrera
2/14/2022 05:59:51 am
Hey guys, have been browsing this forum for the past six months and have learned a lot of valuable information regarding credit. Did some crazy stuff in my late 20s/early 30s but I learned my lesson! Ordinarily, I would have kept it to myself but that will be bad of me the reason I have chosen to let the world know about XAPCreditSolution atGmail dotcom. After I read about them on Reddit and decided to let XAP fix my credit, Fico 8 and Mortgage scores which were (Fico 8 - EQ 635 TU 617 EX 638 and Fico 5 4 2 - EQ 588 TU 588 EX 614) have being raised and collections, charge off, student loans and Credit cards debts have been removed.
Ambrose Metthew
2/18/2022 07:50:24 am
My credit has been down for a long time. I've put off doing anything about it. A week ago, after seeing posts about [email protected] on Trulia, I dropped a messaged at night while I was at work. I wasn’t expecting a reply until the next day, they replied within few minutes, and we put up time to consult over the phone. After a lengthy and informative conversation with them, I felt confident in my decision. Yesterday, I received news that all my collection accounts had been dropped! Dismissed, and removed from my credit report and my score jumped to 799. The hype is real and I'm excited for the future and my improved credit score & financial freedom. Here is their working contact: +1 (424) 307 4562
Michael Wingate
2/18/2022 04:51:17 pm
have been a victim of bitcoin scam about 7 months back. Con artist gained access to my coinbase account through a phishing scam. They stole 2.8 BTC. I was really devastated. I did everything to get back my funds by contacting the support but there was nothing they could do. A friend of my told me about a recovery company name [[email protected]] I wrote them and They help fight against various investment scam and i could only thank God they were able to retrieve my lost funds.
Rosemary Shaw
2/18/2022 06:11:29 pm
There are a lot of untrue recommendations on here and its hard to tell who is legit, i ran into some scammers that ripped me off and I decided I was going to use the last programmer I was going to reach out to and I finally contacted: G O L D C R E D I T F I X @ GMAIL dot com and to my surprise he came though. All the negatives on my credit was expunged permanently and I was able to get a loan to buy a house. If you need your credit boosted to excellent contact GOLD CREDIT FIX toady on this number : + 1 205 291 4665
Mathew Townsend
2/20/2022 04:30:09 pm
Aaron Swartz Cyber Service has been the best credit doctor ever since I get in touch with him. I came up with the idea to increase my credit score and wipe away all negative collections items on my credit report. He raised my score to 790 and also delete the negative items I had within few days. His contact: [email protected]
Harris Richard
2/21/2022 08:49:43 am
How to recover Cyptocurrency ; Binary Option & fake investments RECOVERY Have you ever been a victim of a scam? Have you lost your money to scam imposters online? I implore you to contact this trustworthy hacker and recovery expert DARKSPYACCESS @ gmail. TO HELP RECOVER ALL YOU HAVE LOST, I was a victim of fake people posing as binary options and bitcoin investors, I lost a sum of $4,000 and 2BTC from my bitcoin wallet to these fakes. It took a while before I realized they were scams and this really hurt . Then an in-law of mine heard the incident and recommended to me a specialist with the address - DARKSPYACCESS @ gmail. He helped me recover my stolen bitcoins after providing necessary informations and program requirements and in less than 72hrs the fakes were caught and made to pay for what they did to me .if you have lost any amount to online scams and you're seeking to recover LOST FUNDS from wallet hackers, fake hackers, online dating scams, BTC wallet hack, recovery of lost funds from fake binary investors .Reach out to darkspyaccess recovery to help you ,and you will be so glad you did so, best believe .:.
Caleb
2/23/2022 12:45:30 am
HackWest at Writeme dot COM is considered to be reliable and popular among people who search for trustworthy micro-finance credit repair services. I found him on a credit repair post on Quora as he came highly recommended. After discussing my credit issues with him, he explained in detail how he intended to fix my credit which I consider to be very important in order not to stumble upon scammers because I was once a victim. He fixed my credit, raised my scores to high 810 within a week and I qualified for a home. Super grateful to Hack West. He also did me the favor of recovering my lost funds those miscreants’ scammers stole from me. I highly recommend Hack West to everyone in search of a hacker. You can Whatsapp via 424.307.2638. Cheers!
Steven Joe
2/25/2022 07:56:06 am
A warm greetings to you all reading this my name is Steven Joe; Competence is one thing we don’t need to undermine. TROVIAN CREDIT REPAIR has proved to be competent, reliable and trustworthy. They used their wealth of experience in fixing my bad Credit Report, deleting all negative items including FBI reports and medical bills and bankruptcy from my credit report. They gave me an excellent score of 803 I have no worries anymore I got my life back. Thanks to TROVIANS. I’m sure you won’t have any regret employing the services of TROVIAN. You can always reach them on [email protected] Phone +1 424 307 4562. Have a Great Weekend.
Tina Rhett
3/1/2022 10:33:02 am
I hired XAP Credit because Wells Fargowas reporting late payments on my credit reports from last year when we had anagreement that I would defer payment because of covid. Wells Fargo didn'tcharge me any late fees but reported 6 late payments in my credit reports whichlowered my scores into the 500s. I tried dealing with the credit bureaus myselfand called WF so many times but they never removed the late payments. I triedusing Credit Saint but all they did was dispute and nothing changed. XAP Creditactually called WF and then helped me file a complaint against them with the CPFBand voila - the late payments are now completely gone and my scores are allback to the 790s. Thanks XAPCREDITSOLUTION at GMAIL dot COM!
Tina Rhett
3/1/2022 10:34:14 am
I hired XAP Credit because Wells Fargo was reporting late payments on my credit reports from last year when we had an agreement that I would defer payment because of covid. Wells Fargo didn't charge me any late fees but reported 6 late payments in my credit reports which lowered my scores into the 500s. I tried dealing with the credit bureaus myself and called WF so many times but they never removed the late payments. I tried using Credit Saint but all they did was dispute and nothing changed. XAP Credit actually called WF and then helped me file a complaint against them with the CPFB and voila - the late payments are now completely gone and my scores are all back to the 790s. Thanks XAPCREDITSOLUTION at GMAIL dot COM!
James Barrow
3/1/2022 01:01:31 pm
[email protected]
Scott Jerry
3/1/2022 08:16:11 pm
I just want to show my appreciation to TROVIAN CREDIT REPAIR as promised for helping me fix my credit report. I had an eviction, judgment and quite a number of other negative items on my report with a low 546 credit score. (Mortgage trade lines, Installment trade lines, Revolving credit cards and Auto trade lines) on my report, to my greatest surprise after confiding with TROVIAN all the negative report on my profile were wiped off and my score raised to 809. Now I got the mortgage and I’m very happy. You can contact them on EMAIL: [email protected] cell: +1 (424) 307 4562 for similar problems.
John Albert
3/6/2022 07:51:37 pm
Hi everyone am John Albert, through the help of a credit repair company I got approved for a mortgage loan, my credit score was 456 until I was introduced to TROVIAN by my boss, he had related credit issues, So I contacted them and I paid them a token to get the job done. And to my greatest imagination they raised my score to a high 800 within 7 days, I’m very impressed with their nice work in which they gained my trust. For more info on how you can get your credit fixed kindly reach them [email protected]/ +1 (424) 3074562
Cliff John
3/9/2022 01:40:05 am
We came to the know about the XAPCreditSolution at Gmail dot Com from a Real Estate friend of Danny’s from his Fantasy Football League. Danny was telling him about us wanting to get out of his mom’s house and into a single-family development being built near the high school. Roman, told Danny he had a client with real bad credit like 400 get it up to 775 on his fico with XAP credit repair company in a week. Well, we signed up in January and Danny’s score got us qualified with credit union for the mortgage. I am writing this to tell everyone to use this service and because they will give us $50 credit for referral credits toward our bill. We are referring 2 more people next week.
Bob Harris
3/14/2022 03:02:09 pm
Yosef Schneid
3/15/2022 10:15:09 am
I want to say a Big thank you to Aaron Swartz for repairing my credit report in a different style. He help me to raise my FICO scores to 804 and also paying off my credit card debts on USAA, Capital One card and Amex card. He also cleared student loan and other negative items on credit report in 7 working days. Honest and hardworking hacker. His contact: [email protected]
Heather Walter
3/20/2022 11:45:24 am
GET RICH WITH BLANK ATM CARD ... Whatsapp: +18033921735
Rachael Manor
3/29/2022 07:10:06 pm
I was seeking for a legit credit repair company for a long time, my credit was poor and my family needed a car but we couldn’t afford at the time and all loans I tried to secure got declined not until I came across ( G O L D C R E D I T F I X at GMAIL dot COM ) , He raised my credit score from a poor 526 to an excellent 795 on all 3 bureaus and permanently removed all the negative items on my credit report. If you need a credit repair swiftly I suggest you call or text Gold credit on this line : ( 205 ) 291 4665
Ruben Silva
4/7/2022 11:43:19 am
I just got saved by this credit repair expert called Peter , He permanently removed all the negative credit items I had on my report and boosted my poor score of 581 up to 810. I was finally approved for a loan to buy a truck for my new investment that I have been denied several times due to my bad credit. This is the best thing that has happened to me this year and he could do all of these in 3 weeks. If you also need to boost your credit then I suggest you contact : (CREDITHACKER247 @ GMAIL . COM)
Brittany Cullison
4/9/2022 07:55:14 pm
My Ex fiancé kept deceiving me by telling me I was the only woman in his life and He wanted
Dinesh Parmar
4/12/2022 09:10:51 am
Ever since I heard about GOLDCREDITFIX @ GMAIL . COM from a colleague at work, I made a thorough research about him first before reaching out to him. I have now recommended him to family and friends as they are all satisfied with his credit repair services. In my own case he was able to raise my credit score from poor to an excellent 800 and removed all negatives on my credit in just 1 month . You can call or text him on this line : (435) 319 0883
Jayson Mickey
4/14/2022 06:54:14 am
I have been battling with bad credit report after I lost my job; I couldn’t pay my rent and my landlord filed me for an eviction I was confused on what to do so I confided with my sister she gave me the contact of this wonderful hacker (HACKNET CREDIT SPECIALIST). After i explained all of my worries to him, is like a dream he wiped out all collections, closed account medical bills and cleared my payment history. I’m now free from debts my score is worth talking about I got a new apartment, all thanks to Hacknet. You can fellow him up if you need a perfect credit report. [email protected] or text him 646 450 2754.
August Lucas
4/15/2022 05:13:06 pm
I remember when i needed 2 trucks for my new family business, i got turned down for every loan i applied for because i had a poor credit score of 500 and few negative items impacting my credit . i got frustrated because i kept paying credit companies with no result to show for the thousands of dollars i spent.I came across some good reviews about ACETEAM CREDIT how he has helped a lot of people in the States get their credit improved from poor to excellent and i reached out to him . i contacted him and he increased my score up to 790 and expunged all my negative items . if you need an excellent credit then you should contact - aceteamcredit @ gmail.com
Walter Felix
4/17/2022 11:45:49 pm
Life became very terrible and unfair when you are not able to afford the basic things for your family. Imagine not being able to send your kids to a better school or get a good home, car or loan. Simply because I had a poor credit. I had suffered terribly for the past NINE MONTHS due to a low credit score caused by eviction, collections, late payments and hard inquiries. I had to contact Skyplus760 Credit Solution, a credit repair company. They literally saved me from my traumatizing experience. They increased my score to 815 excellent score and removed the negative and derogatory Items on my credit report. This review is in order to encourage you to do something about your bad credit by contacting (skyplus760 credit compay). It took just 7days for things to change. My life is better now because I can provide for my family. Try them and see your life will never remain the same after using their service, you can Contact them via: Skyplus760 Credit Solution At Gmail Dot Com or Call/WhatsApp (443) 987 6452 and be thankful to me cheers..
Taylor Roland
4/25/2022 04:53:46 pm
I just have to introduce this hacker that I have been working with him on getting my credit score been boosted across the Equifax, TransUnion and Experian report. He made a lot of good changes on my credit report by erasing all the past eviction, bad collections and DUI off my credit report history and also increased my FICO score above 876 across my three credit bureaus report you can contact him for all kind of hacks . Email him here [email protected] go on their website wavedrive.tech for more details,Whatsapp No:+14106350697 if you want to chat them up,One thing i can assure you would not regret this at all he is 100% legit
Elisa Albert
4/28/2022 02:52:35 am
Hello, for two years I had $55,000 in debt, including $23,170 in credit card debt. My credit score was nothing to write home about. I managed to get most of my debt removed in bankruptcy and i was left with $9,000 car loan and $23,000 in student loans. Determined not to repeat my mistakes again I met Hacknet the credit specialist through a credit blog. He helped me clear all my debt and every negative item and also increased my score to an excellent score. I’m recommending Hacknet Credit Specialist for any person in need of credit repairs. Contact him through [email protected]/ (646) 450 2754.
Amilia Robert
5/2/2022 05:19:45 am
If you do not wanna get ripped off, Contact this Chinese hacker at @[email protected] or Whatsapp: +8 (618) 66466_5106 he is fast and do not give excuses. I was trying to save my marriage , My husband was cheating serially and It hurt both me and my kids. This guy gave me proof and I had to leave him even though he was my first love for 15 years. If you decide to hire him, tell him Donna referred you because he's quite selective Thank me later.
Ruby Adams
5/4/2022 05:33:53 am
This is just one of the ways binary option scams can defraud you. There are many fraudulent binary option trading platforms and brokers out there taking advantage of nice investors daily. However, if you’ve fallen victim to a bitcoin scam, there are different steps you can try to get your money back through 'moneyrecovery001 (At) solution4u (Dot) com your best recovery adept when it comes to Binary options
Amilia Robert
5/4/2022 09:38:18 am
My name is Amilia from HOUSTON TX. I just want to say thanks to fast hackers group for helping me unruffled the truth. I suspected my husband
Adams Good
5/12/2022 05:21:32 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Kent Thompson
5/5/2022 02:53:43 pm
Hello everyone, I got my credit report fixed with the help of my co-worker which recommend Aaron Swartz to me. He deleted my IRS and liens from my report and raise my credit score from a low 455 to a high 790. He also clear all debts both bank account and credit cards within few weeks. He is really God’s sent to me. He can help you too. Contact him ; [email protected] ; Cell #: +1(614) 344-8376
Heather Walter
5/6/2022 11:39:15 am
GET RICH WITH BLANK ATM CARD ... Whatsapp: +18033921735
Brookly Fab
5/6/2022 12:15:02 pm
i am super excited this very moment indeed Dr Dominion is truly a good man, i doubted him from the beginning but right now i can trust him with my all because he has put a beautiful smile on my face and change my life from struggle to millionaire, what would i have done without him, just few months ago i was struggling wondering what would my life turn into, now i am here sharing a wonderful testimony of my life, after i explained my whole situation to him he took me as his own daughter and removed my family from shame, he prepared a lottery winning spell for me with true sincerity and gave me a winning number to play and that was how i won that jackpot, Dr Dominion took away my shame, my pain and my worries, what a humble man with a heart of gold, thank you so much i am very grateful for what you have done for me, should you have any interest in giving it a try or going through any difficulties i think he is the right man to talk to and i believe he can help you as well.
Mark
5/6/2022 07:32:36 pm
If you are a victim of a stolen bitcoin or a fraudulent online company which presents itself as a broker or a reliable company but is in fact a scam. Getting your money back isn’t a big deal if you get the right person to help you out but with the rate at which a lot of scammers come online to rip people off, it becomes difficult to get the right person. This why I’m going to recommend to you a legitimate Cyber Investigation guru and recovery expert SPYTECHHUB who has helped binary options victims recover their money back legally. any victims of binary options reading this answer can hire services of professionals to help them get their money back from the internet fraudsters and as well bring them back to justice. quickly search @Spytechhub23 (Spytechhub Private Investigation Services) and request for a recovery of your funds on their page. Fast and efficient!
Green
5/6/2022 07:34:40 pm
Have you lost money while trading forex? Have you tried getting your money out from your binary account and was unable to place a withdrawal? Have you found your self wading through excessively complicated terms which might seem impossible to meet, all because you traded with an unregulated broker? Do not panic, I have good news for you, through the help of a crypto recovery expert ALLHACKINGSOLUTIONS, you can get back all your scammed money using their knowledge, competence and method. Law enforcement authorities always wasting time on case, so you need to use a legitimate recovery expert. If you are a victim or you know any one who is a victim of these occurrences, you should know there are people who can help you. Simply search Allhackingsolutions (Allhackingsolutions Private Hacking Services) send in your request for an outclass help through their page. WhatsApp: +1 415 800 1211
David
5/6/2022 07:43:19 pm
Hi, heard about The Recovery Firm, they specializes in assets and funds recovery. Came across them when my company has issues with our binary options and we almost lost millions in dollars to fake brokers. The Recovery Firm uses distinctive strategies to help recover funds with no legal issues, this has been experienced bcos as the Financial Manager of my company, I had to work closely with The Recovery Firm. They also provide services that involves forex and crypto trading, dating scams also investment management and guides. To contact them EMAIL: Btcsmartrecovery @GMAIL COM, You can simply send an email or Telegram ID:@Btcsmartrecovery and you will be helped to recover 100% of your lost funds. 100% professionalism is their virtue 5/7/2022 01:25:28 pm
I go by the Name Celina Agon Mir from Paris, currently residing here in CA Los Angeles, it's been 9 years have been working here in United State as a Nurse, I always like using Instagram to while away time for myself and I came in contact with a Chinese profile picture, the guy was really awesome and he told me he was into broker trading that I could invest little with $5,000 and within a year i will have enough to buy myself a home and a hospital, so i decided to invest but after 8 months I tried to withdraw and i was asked for more and all this while he encouraged me to keep investing and i had already invested 183k USD with him on his broker platform and we started dating so that really makes me confident in him but it was too late to know I have been scammed after he successfully rip me and put me in a debt of $459k. The night I was to take poison and killed myself I came across ( [email protected] ) and they called me by WhatsApp after which I contacted them firstly, they talked to me and i was calm, less than 72 hours i have heavily restored back better than my normal life... all thanks to almighty great ghostchampionwizard
Adams Good
5/12/2022 05:20:59 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Dahlia Riley
5/9/2022 06:36:51 am
My recommendation to novice bitcoin investors is to conduct your homework before trusting any of these traders with your money. They gain your trust by producing a modest profit, and then when you invest a substantial sum, they block your money for no apparent reason. Thanks to a INSTANT RECOVERY, I was lucky enough to recover approximately 75% of my funds back. If you ever find yourself in a similar scenario, you can contact them at INSTANT RECOVERY 12 AT GMAIL dot coMmM
Collin Brian
5/9/2022 07:21:02 pm
I would like to first thank CYBERTRON for your exceptional service. Thanks to your heroic input I now have my credit back on track. Credit repair companies i signed up with in the past did so little, i was screwed for a long time and continually got turned down on loan and credit applications. Then you were recommended to me by a lady who is your regular client. The money I paid for your services has paid for itself by the great low interest rates I now get. I have told all my friends who are in the same situation that they need to sign up too! My credit is great and for all the newcomers: Yes, there is a light at the end of the tunnel! Go ahead and touch base with the fixer via {CYBERTRONCREDIT (@) GMAIL.COM // WHATSAPP: (512)-240-2493}. Stay woke!
Janice Schuler
5/10/2022 05:35:01 am
I needed a loan for my business .. I needed to do some renovation at my shop and buy more cleaning tools and replace some of the old ones .. Then I applied for a Loan and it was not approved because of some negative reports and late payments I have on my credit ,at this point I was confused on what next to do because I needed this urgently , one of my close friend then brought up this idea of hiring a credit repairer to help me out and I went on to make a proper research on how to get a reliable credit specialist and I ended up working with [email protected] , These guys were like a god sent to me at that point ,everything switched from sorrows to joy within a short period of time , they got me a great score which aided me to get the loan when I reapplied .. don’t waste your time out there anymore , reach out to them as soon as you can .
Adams Good
5/12/2022 05:19:12 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Sam Walter
5/11/2022 05:57:00 am
I remember when i lost $25k to the hands of a scammer i met online. He ripped me off my hard earned money.
Adams Good
5/12/2022 05:20:07 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance. 5/11/2022 08:03:31 am
I go by the Name Celina Agon Mir from Paris, currently residing here in CA Los Angeles, it's been 9 years have been working here in United State as a Nurse, I always like using Instagram to while away time for myself and I came in contact with a Chinese profile picture, the guy was really awesome and he told me he was into broker trading that I could invest little with $5,000 and within a year i will have enough to buy myself a home and a hospital, so i decided to invest but after 8 months I tried to withdraw and i was asked for more and all this while he encouraged me to keep investing and i had already invested 183k USD with him on his broker platform and we started dating so that really makes me confident in him but it was too late to know I have been scammed after he successfully rip me and put me in a debt of $459k. The night I was to take poison and killed myself I came across ( [email protected] ) and they called me by WhatsApp after which I contacted them firstly, they talked to me and i was calm, less than 72 hours i have heavily restored back better than my normal life... all thanks to almighty great ghostchampionwizard
Adams Good
5/12/2022 05:19:39 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
Adams Good
5/12/2022 05:17:44 pm
People cheats due to lack of being contented with their partner or some other reasons. You can't trust your partner 100% cause you get to know different behavior in a person each day. If you suspect your partner is cheating it's better to know the truth at once so you can get the peace of mind before it's too late and you won't live a life full of regrets. You can't do this on your own that's why you need the assistance of an IT expert/PI to monitor and track all the activities of your partner in one swipe. Here is a good news, Zion can simply help you get this info without stress. Are you scared of being ripped off?? You don't need to worry any longer he provides a reliable service, proof before full payment and offers a refund policy which are strictly observed. You can write him at Remotespytech (@) Gmail, com for a wonderful and genuine services. At first, I came across his info on the internet after long search for a genuine help cause I was on a business trip to the UK while my friends in Iowa told me my spouse is seeing someone else I couldn't believe this cause we both trusted each other. I need a quick solution to my curiosity to know the truth cause nothing can be compared to peace of mind, he gave me access to my spouse's phone within 3 hours i contacted him and he got me access to all incoming and outgoing text messages, call logs, WhatsApp, iMessages etc. Then I got to know they've been together for the past few months, are you in a similar situation? Don't wait any longer write Remotespytech (@) gmail,com for a topnotch assistance.
schwartzsoftwarehackins
5/14/2022 07:47:46 pm
Recovery Lost Funds From Online Scammer's/ Cryptocurrency/ Recovery of Stolen bitcoin / Bitcoin Mining/ Increase your Credit score/ MOBILE SPY REMOTECONTROL ACCESS AUTHORIZATION. Removing Bad Records from Both Public and Private database via Email: [email protected] and WhatsApp contact : +16076220782
Claire Wilson
5/15/2022 03:45:09 am
I was able to get my credit cracked and boosted up to 760 with he help of VIRTUALHACKNET AT GMAIL .COM , He’S Indeed a great person to work with, he’s devoted and humble at same time .. I was going through an article when I learnt about him .. then took it to myself to make a research about him before giving out my credentials and Luckily for me it turned out well, my credit was fixed within 2 weeks after reaching out.
David Kern
5/16/2022 05:31:05 pm
I am extremely elated with how CYBERTRON handled my debt crisis. I was certainly over my head and honestly didn’t know where to turn to. There were scores of bad items on my credit, collection and charge offs, a judgment amongst other negatives. As at April 23 my scores were 570, 595, 583. Only 10 days later, I pulled up my report and they are 699, 730 and 733. I am shocked that the scores went up 129, 135 and even a 150 points in such a short time. Luckily I was referred to this specialist by recommendation from a credit repair company consultant. I reached out to him on his Email: CYBERTRONCREDIT @ GMAIL.COM and later on his Official Whatsapp: (512)-240-2493.
Foley Garcia
5/16/2022 07:44:22 pm
I tried paying off some of my credit debts in order to see if my credit score was going to improve in any way yet nothing , it was frustrating at first but I never gave up still , the reason was that I needed to apply for a loan that will aid me buy some heavy tools that I needed at my company , I couldn’t wait any much longer to see if I can try to figure how to fix it on my own so I had to reach out to a credit specialist ,VIRTUALHACKNET@ GMAIL dOT COM is my savior in time of need , they took my credit back up and with that I was able to get the loan and get things in order .. I can’t say much about how good he is till you get work with him and see for yourself .
Vera montero
5/19/2022 08:35:14 am
The very first time I heard about credit hack I couldn’t believe that there was something like that until I got to witness it myself when my credit score Plunged to 764 and most of other credit card debts erased and yes it is permanent , it’s been over 8 months now and it is still intact .. I’m grateful to VIRTUALHACKNET at GMAIL .COM , couldn’t have done it without their team .. you need them ? Then reach out to them .
Richard Reed
5/19/2022 08:53:54 am
Craig Abdie
5/19/2022 11:34:14 pm
I want to thank Jay from XAP Credit Plus for helping me bring my credit score up and for helping me accomplish my first goal that was to get a great credit card like discover and I finally got approved for one! My credit report was in total mess until I contacted XAP via their website (XAPCREDITPLUS.COM) and was attended to without hesitation. I will always recommend XAP Credit Plus.
Brenda
5/20/2022 03:01:28 pm
I got a blank ATM card to withdraw $5k daily for six months. I am so happy about this because i got the cloned atm card after i was scammed twice by fake hackers. I have used the card to withdraw $420k so far. Georg Bednorz Hackers is giving out the cards to help the poor and needy though it is illegal but it is something nice. No one gets caught when using this card. you can get it from Georg Bednorz Hackers today! He is kind, lovely, humble. Also, Georg Bednorz is an expert crypto trader through his trading signals, i made $1 million bitcoins, doubling my profit in 3 weeks.
Ruth Barner
5/22/2022 04:33:18 am
This recovery agent is really God sent. After relating all of my predicaments, details of incidence and necessary requirements for my recovery program, 5/22/2022 08:07:00 pm
Earlier this year i found myself in a situation where my credit got messed up and was unable to qualify for anything good then someone recommended that I contact [email protected] He did a very professional job by helping me raise my credit score up to 785 and he also permanently removed all the negatives on my credit report. i'm amazed with this man's work, he does all kinds of jobs from recovering lost crypto, erasing criminal records, recovering stolen money and all. He comes highly recommended. Thank me later.
CREDIT UTILIZATION
5/23/2022 05:16:41 pm
You’re in absolute control over your credit score, no matter if it’s in the low 400’s or high 700’s. The cost of poor credit is massive. You will pay higher interest rates, require larger down payments, and ultimately life will be expensive compared to one with an excellent credit. The game of credit score ratings never ends hence why I keep my family hacker [CYBERTRONCREDIT @ GMAIL.COM ] close-by. He deletes all negative items (eviction, medical bills, bankruptcy, student loans, judgments, etc.) off credit reports and substitutes them with good tradelines. He repairs credit in 7 business days and on the 8th day you can pull your report and confirm the good changes on your report. He can be reached on the email above or if you prefer texting on Whatsapp: (512)-240-2493. This is a vital information!
Dave Allison
5/25/2022 05:35:43 am
I was scammed by cityinvestgp, I got a message from a trader on my Instagram and told me about how high their profit after investing was, I decided to invest in the online trade but they kept asking for more money including withdrawal fee and it was until then I realized I was being scammed. I couldn't let go because I invested my savings as at that time. I had to make a research on how I could recover my funds from them and I came across the website REMOTESPYTECH (@) GMAIL COM after so many searches. I read several good reviews about the website from various scam victims they have helped and I decided to contact the website admin for help.
Harris Donovan
5/29/2022 04:50:46 am
I’m glad to share my experience working with HackNet Credit Specialist. I had some negative reports of my credit report which really affected me and my family from qualifying for a mortgage at other lenders. I went online and saw people recommending him for his good work and I contact him via mail [email protected]. He cleared all issues relating to my report within a couple of week. If you are having any issues concerning your credit report please CONTACT him with the above email he’s professional and if you also need to qualify for a mortgage with a lender with no lender overlays. Thanks 6/2/2022 09:39:28 am
Premier Funds Recovery are currently collecting funds back for all victims who fall into scams and scams Hurry up and contact him explain your situation to them then will help you and your funds in affordable fees all crypto scam recovery funds, bitcoin scam recovery , investment scam, mobile spy, hacking contact them on ([email protected]) chat him on WhatsApp (+1 (519) 398-1460) I just want to share the good news with people who need help to contact him immediately chat Them
Keiana Brown
6/3/2022 08:36:28 am
Just 1 months ago in 2021, I could not get approved for a loan , a car and a house because my credit score was in the low 400. My loan officer referred me to a credit expert Who removed all the negative items impacting my credit and increased my score on all bureaus to 780. He did all this within 3days and I was really amazed. Now I'm able to buy a house for my family and get approved for loans. You can also reach out to him if you need your credit fixed creditscorehacker @ gmail com.
Heather Walter
6/3/2022 03:37:52 pm
GET RICH WITH BLANK ATM CARD ... Whatsapp: +18033921735
Grey Thompson
6/3/2022 06:41:20 pm
I’ve been investing in Crypto (Bitcoin) for over a year now and I’ve had a lot of money invested on it already. So a couple of weeks ago, suddenly I noticed I couldn’t access my Crypto account. At first, I thought I forgot my password so I tried to reset the password but all to no avail until I discovered my account has been hacked…I was really mad I thought I lost everything cuz I had all my life savings on Crypto.. So I saw a hacker online and I decided to give him a try, I didn’t believe in him at first not until he recovered my Account and my Funds are intact…You can contact him on [email protected] or text him on +1(763) 317-7692..He told me he also fix credit reports and upgrade credit scores..
BEST CREDIT FIXER
6/4/2022 02:47:57 pm
CYBERTRON kept to his promise. I touched base with the specialist early this year and he fulfilled his promise to increase my score and remove multiple negative items on my report. Based on your credit he would recommend how long your credit fix duration should be with him, mine was 10-14 days. At first I was thinking why so short, i was working with a top credit repair company for 8 months without any credible improvement but the it was well worth it because as of today I have A+ credit and I repeat all my negative items have been removed. Credit repair companies and hackers (fallen victim to fakes twice) are all over the place promoting what they can do and but never deliver but from personal experience. His business contacts are [Email: CYBERTRONCREDIT @ GMAIL.COM; and Whatsapp: (512)-240-2493]. He stands alone in the perfect category and delivered 100% of what he said.
Tony Douglas
6/6/2022 04:59:31 pm
I am smiling so big right now, Aaron Swartz help me fixed my credit report within days. He wipe off bad items, criminal records, raise my FICO score from 420 to 800 in 72hrs now I got approved for the loan I applied for and we’re happily living well all thanks to Aaron Swartz he is indeed a credit guru in all rounds. Contact [email protected]
Dennis Beans
6/9/2022 06:07:05 pm
Do you need help on how to monitor and spy your suspected cheating partner? Write ( Remotespytech (at) gmail[]c0m ) for perfect assistance
Dennis
6/9/2022 06:08:09 pm
I was scammed by cityinvestgp, I got a message from a trader on my Instagram and told me about how high their profit after investing was, I decided to invest in the online trade but they kept asking for more money including withdrawal fee and it was until then I realized I was being scammed. I couldn't let go because I invested my savings as at that time. I had to make a research on how I could recover my funds from them and I came across the website REMOTESPYTECH (@) GMAIL COM after so many searches. I read several good reviews about the website from various scam victims they have helped and I decided to contact the website admin for help.
Phil Bailey
6/11/2022 01:40:13 pm
Hi. I once had a credit score of 450. This is due to some late payment on my credit. All efforts to raise my credit score quicker does not yield any result because it is rising slowly even with on time payments. Few months ago I met this credit instructor who helped eliminate those collection on my report and improved my credit score to 845 “excellent When i contacted him he told me to give him 72hours to get through it and I gave the him a try. To my greatest surprise he deleted all the negative information on my credit profile” after we both settled on a deal. What really amaze me was how he got it done, he treats his client like family and go beyond his perimeter to get it done. Contact him if you need a similar service [email protected] OR 724 241-8469
Lucas Freeman
6/15/2022 09:40:56 am
Have you heard about Marketplus247 ?.. Here is a brief on how you can invest and make almost twice as much as you have invested in a smilingly short while.
Chad Murray
6/16/2022 08:05:58 am
I was in distress and in dire need of an upgrade to support my business and family. My FICO scores were really poor and i had numerous doubt till i met CYBERTRON a renowned cyber expert. I really needed this service but I barely trusted the source due to several ripoff attempts on me. To my surprise, he only asked for few info about me and a payment that’s worth the value. after 5days my report came out sound with positive trade lines posted on it including a revolving credit card and a 790 credit score. I really appreciate the selfless work of humanity he does and well worth my recommendation. See for yourself and contact ( CYBERTRONCREDIT @ GMAIL.COM; or Whatsapp: (512)-240-2493). Feel free to use my name as a reference.
Wesley Lenard
6/16/2022 10:44:39 am
I had been to at least 6 finance companies and was turned down by all of them due to my bad report. I gave up on buying a new house. Then a friend told me to contact HACKNET CREDIT SPECIALIST. They told me he’s right one to solve my current situation. I was skeptical, but I called him anyway. This guy is amazing! I gave him all my information and he went to work. Just within a space of 9days he called and told me to check my report I didn’t believe what I saw everything was totally cleaned up and I could go get my dream home, I almost cried. Not only did he fix my credit he also paid off my debts on my credit one and chase bank. I have so much respect for HackNet because of the way he treats his clients, his knowledge of the industry, and his relentless pursuit, I now consider him as the best credit hacker! If you need help, please contact [email protected] or text him +1(646) 450 2754.
Hawk Griffith
6/18/2022 12:52:07 pm
Thanks a lot PINNACLE CREDIT SPECIALIST for the massive job for fixing my credit report without no traces. I was shocked with joy in my heart when he helped me repair my credit report which boost up my FICO score to 805 excellent and removed all the negative items, past eviction, hard inquiries, bankruptcy off my credit report within 8days. He eventually got my job done without charging outrageous fees. Don’t waste your time thinking about any credit specialist. Contact him now: [email protected] phone +1 (585) 466 4373.
Oliver Bangart
6/19/2022 03:10:29 am
We were in severe need of a loan to purchase a car for our family, but my application was denied due to my poor credit score. My credit score was 564 (Transunion), 588 (Equifax), and 591 (Experian) when I checked it. There were several bad entries. After reading so many internet reviews, I decided to go for ROOTKITS CREDIT SPECIALIST as they were highly rated. They assisted me in erasing all of the negative aspects of my life, and increasing my score to excellent across all bureaus and also created good trade lines; they completed all of this within 9 days. You can get in touch with them via:
Amanda Bella
7/2/2022 07:47:19 am
Amanda Bella
7/2/2022 07:48:21 am
Amanda Bella
7/3/2022 03:15:40 am
Smith Brett
7/5/2022 04:01:27 am
I never knew any hacker can be able to recover stolen Bitcoin. I was scammed on a Telegram group early this year by a guy who promised to be paying 80% of my Capital every month. He lured me into investing about $84,000 worth of USDT and they kept telling me to increase my investment before I could withdraw my ROI. Just after I read about Hack West on Reddit, I decided to contact him, few days after my money was recovered. Write West via [email protected] or Whatsapp. + 1 424 307 2638.
George Clifford
7/9/2022 02:59:27 pm
Hi! My name is George Clifford, A truck driver here in Denver .About two years ago I had a divorce and then I lost my Job afterwards. Most of our debts were in my name and I also had child support, I missed out on my payments for months because I was broke then. Right now all my debt has been paid, but the negative items still reflect on my credit score 610, 628 and 624. I applied for an auto loan for my new wife but was declined. I was introduced to Rootkits Credit Specialist by a good friend. They helped me remove the negative items and my score rose to 769, 771 and 775. I’ve been pre-approved thanks to them. You too can testify if you reach out to them on [email protected] or you can call 815 524 8116.
Roger Daniel
7/10/2022 05:46:19 pm
Sincerely there's no quick fix for your credit except you contact the right person and luckily Adrian Lamo got me rejoicing after several try with some wrong people . Adrian Lamo was referred to me by my uncle when I was bitterly battling with my derogatory Credit Report. My score went to 810 from 410 with no negatives and debts... I am so happy I had to come put him out here for who ever might be in need to make smarter financial decisions . Network him via mail [email protected] or via text (413) 551-2034 7/11/2022 11:08:44 am
Hello everyone I know this is not the topic discussing here but with what I Have be through and my bad experience, I want to Please everyone should be careful and stop being deceived by all these brokers and account managers, they scammed me over $500,000 of my investment capital, they kept on requesting for extra funds before a withdrawal request can be accepted and processed, in the end, I lost all my money. All efforts to reach out to their customer support desk had declined, I found it very hard to move on. God so kind I followed a broadcast that teaches on how scammed victims can recover their fund, I contacted him provided for consultation, I got feedback after some hours and I was asked to provide all legal details concerning my investment, I did exactly what they instructed me to do without delay, to my greatest surprise I was able to recover my money back including my profit which my capital generated. I said I will not hold this to myself but share it to the public so that all scammed victims can get their funds back. Chat Them on WhatsApp (+31 6 84990027). Reach him on Instagram: @wizardwierzbickiprogrammer
George
7/15/2022 10:27:03 pm
Bitcoin recovery expert needed? Hello, have you ever been scammed online by fake binary options or have you invested in the wrong platform and you cannot withdraw your funds back or get your invested funds with profits. You do not need to worry about that anymore. We at cryptorefunder360(@)gmail(.)com are a team of hackers that help in recovering scammed cryptocurrencies. Have you been scammed of you money and you’d like to get it back? Contact us now and let us recover your funds back to your hands. Email us Cryptorefunder360(@)gmail(.)com or WhatsApp +1 (681) 253 0702 now.
Nathan Miller
7/18/2022 03:13:45 pm
A few weeks ago i got acquisition of a 2019 choice car well at 2.9%, rather than 19% as per my last car purchase before help from 'CYBERTRON'. However this purchase as well as the BANK loan for a business would NOT have been possible without him. He got busy from day 1 of hiring him and relentlessly pursued the creditors, and made them VERIFY any and all credit that was supposedly established in my name, and the credit that could NOT be verified, was deleted from my credit report ! ALL THREE reports ! ((unlike other credit repair companies or hackers whom I’ve hired and got absolutely NO results)). I have been able to enjoy the Privilege of good credit once again, and I have actually been able to monitor and see my score going up, and the derogatory credit dismissed from the bureaus. So in closing don’t get discouraged about your current credit debacle, i wallowed in it for too long until i touched base with this Life-Saver via [Email: CYBERTRONCREDIT at GMAIL dot COM].
Burton Howard
7/27/2022 10:06:44 am
Do you need professional help if you’re trying to fix your bad credit report, I got a quick and fast credit improvement after contacting Hacknet Credit Specialist and he delivered a perfect job for me by removing all my negative items tax liens bankruptcy late payment including the criminal history on my public record and improve my score to excellent 810 only within a short time of using his service. You can as well contact him directly through. ([email protected] or cell +1 646 450 2754) and be rest assured of a permanent job. Comments are closed.
|
Archives
September 2019
Categories
All
|
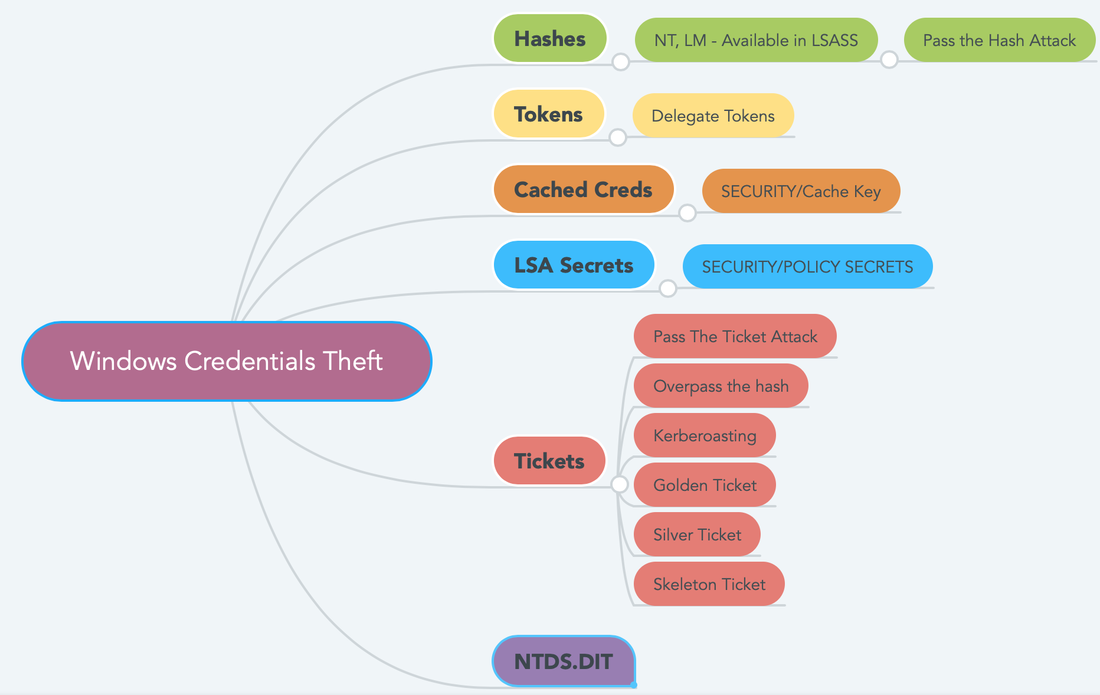
 RSS Feed
RSS Feed